GSM Data Receiver Scams: How They Work, the Risks, and How to Stay Safe
In the ever-evolving landscape of cybercrime and financial fraud, GSM data receiver scams represent a sophisticated blend of technology and deception. These scams revolve around devices that wirelessly capture and transmit sensitive credit and debit card information, often without the victim even realizing they’ve been targeted. As we delve into this topic, it’s crucial to understand that while knowledge empowers prevention, any attempt to engage in or facilitate such activities is illegal and carries severe consequences. This article aims to educate readers on the mechanics of these scams, their prevalence, and practical steps for protection, drawing from expert analyses and real-world insights.
GSM, or Global System for Mobile Communications, is the standard for mobile networks worldwide. When applied to data receivers in the context of fraud, it enables thieves to skim card details remotely, bypassing the need to physically retrieve devices from compromised ATMs or point-of-sale (POS) systems. The scams aren’t just about using these devices; they also include fraudulent sales of purported “GSM data receivers” online, where scammers prey on aspiring criminals or naive buyers. According to cybersecurity experts, skimming incidents, including those involving GSM technology, cost financial institutions and consumers billions annually. This article will explore the technology behind these devices, how scams unfold, warning signs, legal ramifications, and actionable defense strategies, ensuring you gain a comprehensive understanding.
What is a GSM Data Receiver?
At its core, a GSM data receiver is a specialized skimming device that integrates cellular technology to capture and relay stolen data. Traditional skimmers are small overlays placed on ATM card slots or gas pump readers, which read the magnetic stripe on cards as they are swiped. These older models require the fraudster to return to the site to collect the device and extract the data, increasing the risk of detection.
GSM-enhanced versions elevate this threat by incorporating a SIM card and GSM module, allowing real-time transmission of captured data via SMS or data packets to a remote phone or server. This wireless capability means the scammer can receive stolen card numbers, expiration dates, and sometimes even PINs (if combined with a hidden camera or keypad overlay) from miles away. The device typically consists of a compact circuit board, antenna, battery, and memory storage, disguised to blend seamlessly with the ATM’s exterior.
For instance, a typical GSM skimmer might be installed in under a minute by attaching it over the card reader slot. Once in place, it intercepts the card’s magnetic stripe data during transactions. A separate component, like a pinhole camera hidden in a brochure holder or a fake keypad overlay, captures the PIN. The GSM module then sends this information instantly, reducing the window for law enforcement intervention.
To visualize this, consider the following:
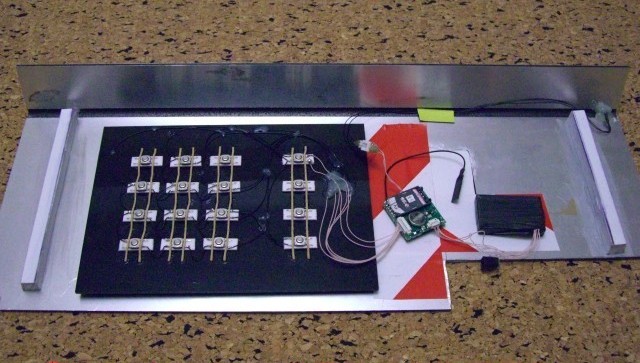
This image illustrates a GSM-based skimmer device, highlighting its compact design that makes it hard to detect.
The appeal of GSM technology in skimming lies in its efficiency and safety for the perpetrator. As one analysis notes, without the need to revisit the ATM, fraudsters avoid surveillance cameras or patrols that might catch them in the act. However, this technology isn’t foolproof; signal interference, battery life, or network issues can disrupt operations, though advanced models mitigate these with better components.
How GSM Data Receiver Scams Work
GSM data receiver scams operate on two primary levels: the direct theft of card data and the secondary scam of selling fake or ineffective devices to would-be criminals.
Direct Data Theft Scams
In the theft scenario, fraudsters target high-traffic ATMs, such as those in convenience stores, gas stations, or standalone kiosks. The process unfolds in steps:
- Installation: The scammer attaches the skimmer to the card reader. For GSM models, this includes ensuring the device has a charged battery and a working SIM card for transmission.
- Data Capture: As users insert or swipe their cards, the skimmer reads the magnetic stripe or, in some cases, the EMV chip (via “shimming” for chip cards). A hidden camera or fake keypad records the PIN.
- Transmission: Captured data is sent via SMS to the fraudster’s phone. In sophisticated setups, data is encrypted or batched to avoid detection.
- Exploitation: The thief clones the cards onto blank magnetic stripe cards and uses them for fraudulent purchases, cash withdrawals, or online transactions.
This method is particularly dangerous because it can affect dozens or hundreds of victims before the device is discovered. Reports indicate that GSM skimmers have been used in organized crime rings, with data sold on the dark web for as little as $10 per card.
The above illustration depicts a common ATM skimming setup, showing how the device overlays the legitimate reader.
Secondary Sales Scams
A more insidious layer involves online marketplaces or shady websites selling “GSM data receivers” to aspiring fraudsters. Sites like gsm-receiver.com have been flagged as scams, where sellers promise high-tech devices capable of effortless data theft but deliver non-functional gadgets or nothing at all. These scams target individuals lured by quick riches, often through forums, social media, or dark web ads.
Buyers are instructed to pay via untraceable methods like cryptocurrency or wire transfers. Once payment is made, the seller ghosts the buyer or sends a cheap, ineffective device. In some cases, the “product” is a DIY kit with outdated components that fail to work, leaving the buyer out of pocket and potentially exposed to law enforcement if they attempt to use it.
Another variant includes “post officer and police scams,” where fraudsters send packages with tracking to fake addresses, then impersonate authorities to extract more money from victims under the guise of resolving delivery issues.
These sales scams exploit the underground economy, where trust is minimal, and victims rarely report to authorities due to the illegal nature of their intent.

Real-World Examples and Prevalence
GSM data receiver scams have made headlines globally. In 2010, cybersecurity researcher Brian Krebs detailed how GSM skimmers were revolutionizing ATM fraud by allowing remote data retrieval, citing cases where thieves harvested thousands of dollars without returning to the scene. More recently, in 2020, reports emerged of wireless skimmers that could clone cards without physical attachments, using proximity readers.
In the U.S., the FBI has warned about skimming at freestanding ATMs, noting devices that fit over card readers or along cables. A 2022 Microsoft report on toll fraud malware highlighted how mobile networks are exploited for billing scams, drawing parallels to GSM data transmission in skimming.
Internationally, in countries like India and Nigeria, where mobile penetration is high, GSM gateway frauds (a related issue) cause massive revenue losses to telecoms by bypassing legal interconnects. A 2019 study estimated such frauds as a national security threat due to their scale.
In Michigan and New York, state departments have issued alerts on skimming and shimming, emphasizing the shift to chip-reading devices. Social media posts from law enforcement, like those from the Los Angeles County Sheriff’s Department, estimate skimming costs over $1 billion yearly.
These examples underscore the global reach and economic impact, with victims ranging from individuals losing hundreds to banks facing class-action lawsuits.
Signs of a GSM Data Receiver Scam
Recognizing these scams requires vigilance. For direct theft:
- Physical Anomalies: Inspect ATMs for loose parts, bulky card slots, or unusual attachments. Tug gently on the reader; if it wobbles, it might be a skimmer.
- Hidden Cameras: Check for pinhole lenses in nearby fixtures.
- Transaction Issues: If your card doesn’t swipe smoothly or the machine behaves oddly, abort and report it.
For sales scams:
- Too-Good-to-Be-True Offers: Websites promising easy money with minimal risk are red flags.
- Payment Methods: Demands for crypto or wire transfers indicate fraud.
- Lack of Verification: No customer reviews, anonymous sellers, or domains flagged on scam watch sites like ScamWatcher.
This graphic outlines common warning signs of credit card fraud, including skimming indicators.
Additionally, monitor your accounts for unauthorized transactions, a telltale sign of compromise.
Legal and Ethical Implications
Engaging in GSM data receiver activities is unequivocally illegal. In the U.S., skimming violates federal laws like the Electronic Funds Transfer Act and can lead to charges under wire fraud statutes, with penalties up to 20 years in prison and hefty fines. Internationally, similar laws apply, often compounded by telecom regulations.
Ethically, these scams erode trust in financial systems, disproportionately affecting vulnerable populations like the elderly or low-income users. Banks invest millions in countermeasures, costs passed to consumers via fees. Moreover, buying such devices, even if scammed, implicates one in attempted fraud.
From a broader perspective, these crimes fund organized crime, including terrorism or drug trafficking. Awareness articles like this emphasize education over exploitation, aligning with ethical boundaries in cybersecurity discourse.
How to Protect Yourself: Practical Steps
Prevention is key. Here’s a step-by-step guide:
- Use Secure ATMs: Opt for bank-owned machines inside branches, which are monitored more closely.
- Adopt Chip Technology: EMV chips are harder to skim than magnetic stripes; always insert rather than swipe if possible.
- Cover Your PIN: Shield the keypad with your hand to block cameras.
- Monitor Accounts: Set up alerts for transactions and review statements weekly.
- Use Contactless Payments: Apps like Apple Pay or Google Wallet add encryption layers.
- Report Suspicious Activity: Contact your bank immediately if something seems off; they can freeze accounts.
- Avoid Shady Purchases: Steer clear of online offers for skimming devices; report them to authorities like the FTC or FBI.
- Educate Others: Share knowledge with family and friends to build community vigilance.
For businesses, install anti-skimming tech like encrypted readers or regular inspections.
In cases of victimization, file reports with local police, your bank, and credit bureaus to place fraud alerts.
Conclusion
GSM data receiver scams exemplify how technology can be weaponized for fraud, blending wireless innovation with criminal intent. By understanding their operations from installation to data exploitation and recognizing red flags, individuals can fortify their defenses against these threats. Remember, the best protection is a combination of awareness, technology, and proactive habits. As financial landscapes evolve with digital wallets and biometrics, scams will adapt, but informed users remain the strongest barrier.
Stay vigilant, and if you suspect a scam, report it promptly. Knowledge not only protects your wallet but also contributes to a safer digital ecosystem for all.
In today’s digital age, vigilance is key to safeguarding yourself from scams. A group of individuals has initiated scams targeting those interested in GSM data receivers, and it’s important to be aware of these fraudulent schemes. Here, we’ll shed light on three of the most prevalent GSM Data Receiver scams:
- Fake Company Employees: Scammers exploit the good reputation of legitimate companies, such as ours, to deceive potential customers. They pose as employees, promising attractive prices and soliciting payments, only to vanish without delivering. Beware of deals that seem too good to be true, as authentic devices are never sold for unrealistically low prices.
- The Fake Escrow Scam: Many scammers operate dual websites. One offers skimmers for sale, while the other presents a “fake escrow” service. When asked for proof of legitimacy, they direct you to their escrow platform, which is designed to trap your funds. Depositing money with them leads to blocked communication and lost money.
- The Post Officer and Police Scam: Scammers employ a sophisticated ruse in which they send a package with a tracking number to a nonexistent address in your vicinity. When the package appears to be held up at the post office, they contact you, claiming that the police or customs have seized it. They demand an ‘800-1000 USD donation’ to release your order, initiating a cycle of extortion and creating anxiety about your security.
- Fake Websites with Watermarks: Beware of websites that steal product images and descriptions and place non-transparent watermarks over them to hide the original ones. Always ensure that watermarks are transparent, as a lack of transparency may indicate stolen resources. These websites typically sell products at unusually low prices.
- Many Similar Websites with Low Prices: Scammers often create multiple websites, typically 5-10, with minor variations but the same style to attract a larger audience. They duplicate content, so if you come across several similar websites when searching for a product at a low price, exercise caution.
We will continue to share these stories to keep you informed and help prevent scammers from stealing your hard-earned money. We understand that such posts may affect us, and scammers may resort to posting negative reviews to harm our reputation. However, we trust that those familiar with this market will be able to discern fact from fiction. We have a worldwide community of satisfied customers who continue to support us, and we’re committed to educating you and combating scammers.
Remember, When you are worthy of immulation, their will arises a batllion of counterfeit you, We may have a number of other sites mimicking us. Stay informed, stay vigilant.