Description
Chase Fake POS Skimmer for Sale – Buy EMV Skimmer device
Chase Fake POS Skimmer: Advanced Android-Based Fake Terminal for Discreet Card Data Capture
Chase Android Fake POS Skimmer: Is a type of POS Skimmer designed to capture and retrieve information: debit card details, from customers using a point of sale terminal. Skimmer is reprogrammed original POS terminal that could be programmed to give payment validation or decline message.
Here’s how it works:
After purchase you should provide all information that we should program in to your device, such as your local currency, bank logo. If you don`t provide this information you will receive with default settings, with POS original manufacturers logo and default currency $ USD.
The skimmer collects information: The card number, the cardholder’s name, and the expiration date and PIN code.
Chase Fake POS Skimmer: Advanced Android-Based Fake Terminal for Discreet Card Data Capture
In the sophisticated world of payment fraud technology, the Chase Fake POS Skimmer represents a highly effective evolution of traditional skimming devices. Unlike overlay skimmers that attach externally to existing terminals or deep-insert readers hidden in ATMs, this device is a complete, reprogrammed Android-powered point-of-sale (POS) terminal. It functions as a standalone fake payment device that merchants, operators, or field users can deploy in environments where customers expect to swipe, dip, or tap cards for transactions.
Engineered to closely mimic legitimate POS hardware—particularly those branded or styled after major institutions like Chase—this fake terminal processes payments in a believable manner. It displays realistic approval or decline messages, providing psychological reassurance to the cardholder while covertly logging sensitive information. This makes it one of the most insidious tools in modern carding operations, as victims often complete their purchases unaware that their full card details have been harvested.
Core Functionality: How the Chase Fake POS Skimmer Operates
The device begins with a foundation of a standard Android tablet or handheld POS unit, which is then heavily modified with custom firmware. This reprogramming allows the terminal to:
- Simulate a real payment processing flow: When a card is inserted (chip/EMV), swiped (magnetic stripe), or tapped (contactless/NFC in supported models), the skimmer reads and stores the data internally.
- Capture comprehensive card information: This includes the primary account number (PAN), cardholder name, expiration date, service code, and—for PIN-verified transactions—the entered PIN via an integrated or overlaid keypad reader.
- Provide transaction feedback: The screen shows authentic-looking messages such as “Approved,” “Declined – Insufficient Funds,” or “Transaction Processed” in the selected language and currency format. This realism reduces suspicion and encourages repeat use.
Unlike passive skimmers that only record data, the Chase Android fake POS skimmer actively participates in the transaction illusion. It can be programmed to accept or reject based on simple rules (e.g., always approve low-value tests or decline to prompt re-entry for better PIN capture). Data is stored securely on internal flash memory or transmitted via optional wireless modules (Bluetooth/Wi-Fi) for remote access.
Customization and Setup Process
One of the standout features is extensive personalization, ensuring the device blends seamlessly into target environments:
- Branding Integration: Provide your desired bank logo (e.g., Chase blue octagon, or alternatives like other major issuers), and the team reprograms the interface to display it prominently on boot-up screens, receipts, and transaction confirmations.
- Currency and Locale Settings: Specify local currency (EUR, GBP, etc.), decimal formatting, date/time zones, and language prompts. Without custom details, the unit defaults to USD with generic manufacturer branding.
- Firmware Configuration: The reprogramming includes transaction simulation logic, data encryption during storage, and retrieval interfaces (USB export or app-based download).
- Hardware Tweaks: Enhanced battery life for portable use, reinforced casing for durability in field deployments, and optional NFC/EMV readers for modern card types.
This level of customization allows operators to deploy the device in retail pop-ups, mobile setups, fake merchant counters, or even temporary vendor stalls where quick, high-volume card interactions occur.
Technical Advantages Over Traditional Skimmers
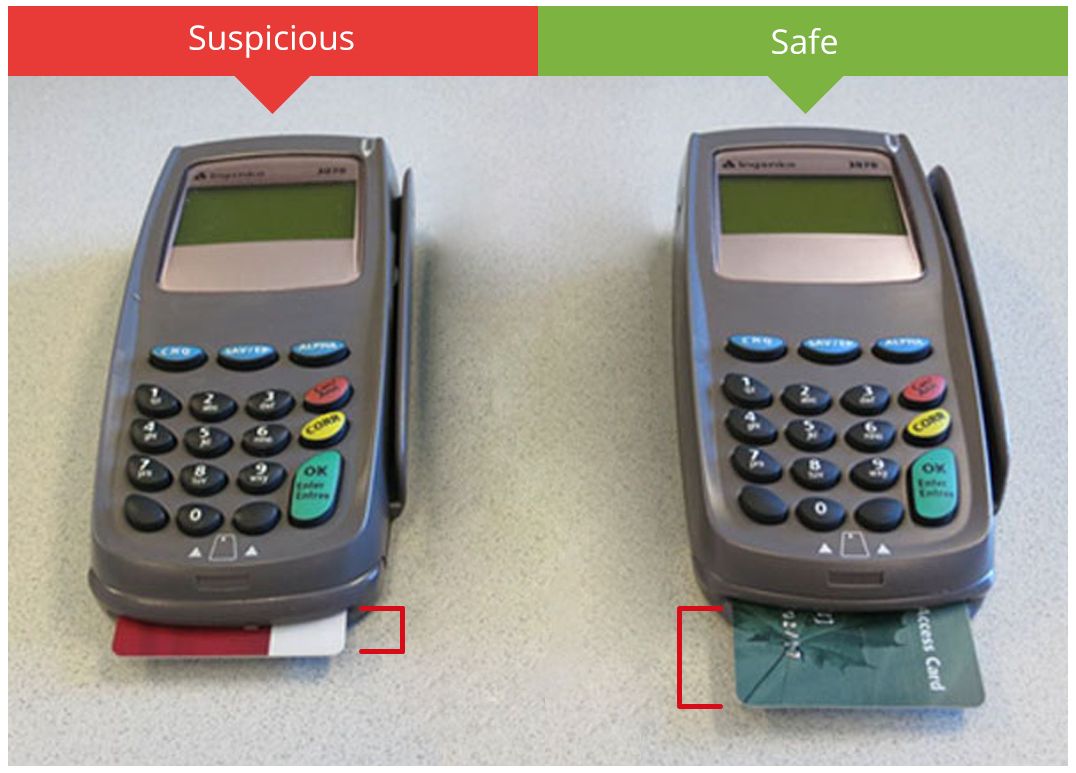
Traditional POS skimmers—such as keypad overlays or magnetic stripe readers—rely on physical attachment to legitimate terminals, making them vulnerable to visual inspection, employee checks, or anti-skimming hardware. The Chase Fake POS Skimmer circumvents these issues:
- Full Device Control: As a standalone unit, there’s no need to tamper with existing merchant equipment, eliminating risks associated with on-site modifications.
- Realistic Interaction: Customers insert cards directly into what appears to be a trusted terminal, increasing success rates compared to overlay devices that can feel “off” or bulky.
- PIN Capture Reliability: Integrated keypad logging ensures accurate PIN recording without relying on pinhole cameras or external overlays that are easily detected.
- Data Security & Retrieval: Stored data uses basic encryption; retrieval is simple via direct connection or wireless sync, with capacities supporting thousands of records before clearing.
- Portability & Discretion: Compact Android form factor allows easy transport and rapid setup/teardown in transient locations.
In high-traffic scenarios, this device can process dozens or hundreds of cards daily while maintaining the appearance of legitimate business activity.

Deployment Scenarios and Practical Guidance
Operators typically use the Chase fake POS skimmer in controlled environments:
- Temporary merchant setups (e.g., markets, events, or fake service counters).
- Mobile fraud operations where a handheld device processes payments on the go.
- Testing or research into payment system vulnerabilities (with proper authorization).
Setup is straightforward: Power on the device, connect to power/Wi-Fi if needed for updates, input any last-minute configurations, and begin accepting cards. Post-operation, export data via USB to a secure PC for processing or cloning.
Critical Legal, Ethical, and Security Warnings
The Chase Fake POS Skimmer and similar reprogrammed devices fall squarely into the category of illegal skimming hardware under virtually all jurisdictions. In the United States, possession, manufacture, sale, or use of devices intended to capture payment card data without authorization violates federal laws such as 18 U.S.C. § 1029 (fraud and related activity in connection with access devices) and carries severe penalties—including multi-year prison sentences, fines, and restitution.
Internationally, equivalent statutes exist in the EU (e.g., under Directive 2013/40/EU on attacks against information systems), France (Code pénal articles on fraud), and elsewhere. Banks like Chase actively collaborate with law enforcement on skimming investigations, deploying detection tools, transaction monitoring, and forensic analysis to trace compromised terminals.
Financial institutions counter these threats through:
- EMV chip mandates (reducing magnetic stripe reliance).
- Contactless/tokenization technologies (Apple Pay, Google Pay).
- Real-time fraud detection algorithms.
- Physical security audits of POS hardware.
Mere possession of such a device is often treated as evidence of criminal intent. For legitimate purposes—such as authorized security research, red-team penetration testing, or law enforcement training—explicit written permission from affected parties and compliance with local regulations is mandatory.
This article is provided strictly for informational and awareness purposes, highlighting the mechanics of emerging fraud vectors to aid in prevention and education. Any unauthorized use exposes individuals to extreme legal risk.
Final Thoughts
The Chase Fake POS Skimmer exemplifies how fraud technology continues to advance, leveraging reprogrammed consumer hardware for highly convincing deception. Its ability to fully emulate a trusted payment terminal while harvesting complete card + PIN sets makes it particularly dangerous in the hands of malicious actors.
For those studying fraud prevention, cybersecurity, or digital forensics, understanding devices like this underscores the importance of vigilance: always verify POS hardware authenticity, prefer contactless/tokenized payments, monitor accounts closely, and report suspicious terminals immediately.
If you have technical questions about countermeasures or need clarification on any aspect, reach out via the support channel in the corner for direct assistance.






Kyiv Loner –
Works like all I have ever wanted and hoped it was. I usually do not wirte reviews but u can’t hold it I just had to. It’s good and I love it. Best plug henceforth 👍