The Under ground truth about GSM Data Receiver V5.2 Skimmer
We completely can say GSM Data Receiver is our bestseller. This is most powerful GSM Data Receiver and best skimming tool currently.
True be told, you must be very careful when buying GSM Data Receiver. So Many scammers from India and Africa are fooling people with our product. They made websites and listed our product as low as 200 or 400$. Somebody sell it for 600$. Remember simple thing if it is too good to be true mostly it is scam.
Around 90% of our buyers know us and come by recommendation from other customers who bought something from us and know how we are working, this message is for those people who never bought anything for us. Our recommendation is be super careful. If you haven’t gotton any recommendation from previous buyer it simply means that at the moment you have no contact with those already cashing out from our softwares and hardwares. Here is the good news you can be the next to recommend others after cashout.

Explore all you need to know about GSM Data Receiver V5.2 Skimmer
In the landscape of financial cybercrime as of January 2026, few devices have generated as much underground discussion as the GSM Data Receiver series—particularly the V5.2 variant. Marketed in shadowy online forums and dark web marketplaces as an advanced, contactless skimming solution, the GSM Data Receiver V5.2 is promoted as capable of intercepting credit/debit card information—including magnetic stripe tracks, EMV chip data, and PINs—from ATMs and point-of-sale (POS) terminals without any physical connection to the machine.
Unlike traditional overlay skimmers that require direct attachment to the card reader, this device allegedly operates wirelessly, scanning for vulnerable bank network communications over GSM frequencies and relaying captured data in real time via SMS or mobile data. Sellers claim ranges of 50–300 meters (depending on environment and antenna configuration), with built-in memory for thousands of records and USB download capabilities.
While these claims circulate widely in carding communities and illicit sales listings, it’s critical to emphasize upfront: manufacturing, possessing, distributing, or using such a device constitutes serious criminal activity in virtually every jurisdiction worldwide. In the United States, for example, it violates federal laws including 18 U.S.C. § 1029 (fraud and related activity in connection with access devices) and can result in multi-year prison sentences and substantial fines. Similar prohibitions exist under EU cybercrime directives, INTERPOL frameworks, and national laws in countries like Nigeria, where financial fraud is aggressively prosecuted.
This article provides an educational overview of what is publicly alleged about the GSM Data Receiver V5.2, its purported technical specifications, historical context within ATM/POS skimming evolution, reported real-world impacts, detection challenges, and—most importantly—practical, lawful countermeasures that financial institutions, merchants, and consumers can implement. The goal is awareness and protection, not endorsement or instruction in illegal activity.
A conceptual illustration of a compact wireless skimming device hidden in everyday carry items, representing the stealth claimed by sellers of GSM receivers. EMV Shimmer for Sale
What is the GSM Data Receiver V5.2?
Promotional materials describe the V5.2 as the latest iteration (updated in 2024–2025) of a hardware-software bundle originally popularized around 2015–2018. Key alleged features include:
- Wireless interception — Scans GSM/LTE frequencies used by some older or poorly secured ATM/POS communication modules.
- Extended range — Up to 50–75 meters through walls (claimed 300 m line-of-sight with upgraded antennas).
- Data captured — Track 1 & 2 (magnetic stripe), dynamic EMV data, PIN (via alleged side-channel or network sniffing), cardholder name, ZIP, balance hints, and transaction metadata.
- Storage & transmission — 32–64 MB internal memory (storing 50,000–100,000 records), real-time SMS relay to operator’s phone, USB interface for bulk download.
- Battery life — 3.7V 2500 mAh rechargeable, 12–18 hours continuous operation.
- Physical size — Approximately 50 × 40 mm main board + 170 mm antenna; fits in pockets, bags, or vehicles.
- Software — Windows-based V5.2 interface for frequency tuning, data decoding (hex to readable format), and log management.
Sellers differentiate generations by antenna count (single vs. dual) and software compatibility. The V5.2 update reportedly includes improved signal decoding, better EMV handling, and obfuscation against basic antivirus detection on the control PC.
Representative diagram of a wireless receiver setup near a target ATM, showing the claimed passive interception method (for illustrative purposes only).

Historical Evolution of GSM-Based Skimmers
GSM receivers emerged prominently in the mid-2010s as criminals sought alternatives to physical skimmers after widespread EMV adoption reduced magnetic stripe fraud effectiveness. Early versions (circa 2015) exploited unencrypted or weakly protected GSM modem communications in certain ATM models, particularly in regions with legacy infrastructure.
By 2020–2022, variants appeared claiming partial EMV cracking via dynamic data capture during transaction handshakes. The V5 lineage (V5.0 → V5.2) reflects iterative improvements in antenna sensitivity, battery efficiency, and software for decoding obfuscated packets.
In 2025–2026, these devices remain discussed in carding forums despite law enforcement crackdowns. Many listings warn of scams—prices range from $1,200–$5,000+, yet hardware analysis by security researchers suggests much of the “magic” relies on outdated vulnerabilities that major manufacturers have patched.
How It Is Alleged to Work (Conceptual Overview)
Sellers describe a multi-step process:
- Placement — Operator positions the device within range (vehicle, backpack, nearby building) of target ATMs/POS terminals.
- Frequency scanning — Software tunes to GSM bands (850–1900 MHz) used by bank terminals for authorization or telemetry.
- Interception — Captures unencrypted or weakly encrypted data packets during card transactions.
- Decoding & storage — Onboard firmware or PC software converts raw signals into card/PIN records.
- Retrieval — Real-time SMS alerts or later USB dump.
Important caveat: Modern EMV implementations use strong session-specific cryptography (ARQC/ARPC), making reliable PIN + full chip data capture extremely difficult without additional compromises (e.g., shimming + camera, or network-level MITM). Claims of effortless EMV + PIN interception are widely disputed by independent cybersecurity experts.
Real-World Trends and Impacts in 2026
ATM-related fraud statistics from 2025 (carried into 2026) show wireless skimming as a smaller but persistent vector compared to jackpotting (71% of incidents) or deep-insert physical skimmers. Losses from all skimming forms exceed hundreds of millions annually, though exact attribution to GSM receivers is hard due to under-reporting and scam devices flooding the market.
High-profile cases often involve hybrid attacks rather than pure wireless methods. Organized groups in Eastern Europe, Latin America, and parts of Africa continue experimenting with these tools, but successful large-scale operations increasingly rely on physical access combined with malware.
Victims suffer direct financial loss, identity theft, and recovery burdens. Banks face reimbursement costs, reputational damage, and regulatory pressure.

Prevention and Mitigation Strategies
Defending against alleged wireless skimmers requires layered security:
- For consumers
- Use contactless/mobile payments (Apple Pay, Google Pay) – tokenization renders intercepted data useless.
- Prefer indoor, bank-branched ATMs with modern hardware.
- Enable transaction alerts and monitor accounts daily.
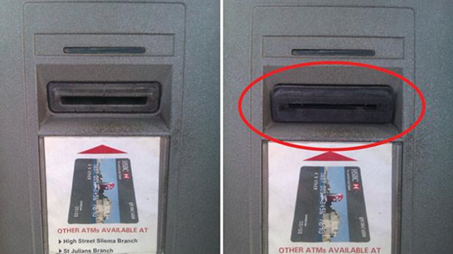
- Cover PIN entry and inspect machines for tampering.
- For financial institutions & merchants
- Upgrade to fully encrypted end-to-end communication (no legacy GSM modems).
- Implement network segmentation and anomaly detection for ATM/POS traffic.
- Deploy anti-skimming hardware (jammers where legal, shielded readers).
- Regular physical inspections + AI-powered camera surveillance.
- Broader measures
- Phase out magnetic stripe fallback entirely.
- Adopt stronger authentication (biometrics, push-to-phone confirmation).
- Collaborate with law enforcement for threat intelligence.
Modern ATM security features: reinforced card readers, anti-skimming overlays, and surveillance integration—key defenses against evolving threats.
Legal and Ethical Considerations
Attempting to acquire, test, or deploy a GSM Data Receiver V5.2 (or any skimming device) is a felony in most countries. Penalties include imprisonment (5–20+ years), asset forfeiture, and international extradition risk. Even “research” purchases can trigger money laundering or conspiracy charges.
Ethically, these tools directly harm individuals often the most vulnerable who rely on cash access. Security researchers study them only in controlled, authorized environments to develop better defenses.

ATM Jackpotting Black Box For Sale
Conclusion
The GSM Data Receiver V5.2 represents a chapter in the ongoing arms race between cybercriminals and the financial security industry. While marketed as a revolutionary wireless tool, its practical effectiveness in 2026 is limited by widespread patching of legacy vulnerabilities and the superiority of contactless/tokenized payments.
The most effective response remains education, vigilance, and investment in modern security architecture. By understanding the claims—and more importantly, the realities—of devices like the V5.2, we strengthen collective defenses against financial fraud.