Free Shipping Bonus
Worldwide free shipping and instant software delivery
Best prices
We offer lowest prices for our products
Discreet package
We guarantee delivery to your doors without customs fees
What you need to know about our EMV Skimmer
Our Business
For nearly 8 years, Global EMV Cloned Cards has remained a leading developer and provider of equipment for card personalization, EMV compliance/migration, smart card manufacturing and semiconductor handling equipment.
Our solutions and products address the requirements of a range markets worldwide: Financial EMV/Chip Card, TSM, Restaurant Management Systems, banking services, Government/Secure ID, Healthcare/Insurance, and Corporate markets.
We offer our SDR GSM Skimmer for rent! Pay half of total amount as down payment and receive the merchandise shipped next to your door step! Rent fee is 10% of your 90-days profits you gain, that means you will have to pay us 10% of your profits at every 90-days time period. Interested? Contact US Now
Buy ATM SKimmer
Our U.S.-made skimmers are so great — you’ll want to come back for more after your first purchase! Our ATM skimmers, including top models like Diebold and NCR, come with sleek Magnetic Heads and options like MSR010 and MSR009. They also offer USB, Bluetooth, or GSM features for sending dumps and pins via SMS. The GSM Data Receiver Skimmer connects wirelessly to bank frequencies around the world we offer free worldwide shipping with tracking and guarantee delivery within a week, or we’ll refund you. If you have any questions, our support team is available 24/7 at support now.
Buy ATM Insert Skimmer
Insert Skimmer device is a unique card copy system that is placed in the center of ATM Card Reader. It is impossible to notice from the outside. It can detect this device only if the ATM alarms or the bank officer looks inside the ATM.
This model: NCR Small Insert Skimmer device is approximately 4.1 centimeters in size. It is a device that is easily placed in ATMs and difficult to spot. Device is able to store on board more than 50,000 credit cards tracks data. It also come with a special software developed by our IT Engineers that will help you to export tracks data into your PC and also Erase old data from device. Total device memory is 64 MB.
– Software is compatible with all manufactured skimmers by us (Deep Insert, Small Insert – NCR, Diebold, Wincor)
— Our packs offer everything you need to collect data (cables, pin pad, software). Plus, we offer guidance through our special support teams that are assigned to customers that are out on the field. That means you can talk in real time with support while on the field.
ATM Insert Skimmer: The Fraud Device You Can’t See
ATM skimming didn’t end when bulky card overlays disappeared. Instead, it moved inside the machine. The ATM insert skimmer is one of the most discreet forms of payment fraud still in use today, and it works precisely because most people don’t know it exists.
Unlike external skimmers that attach to the front of an ATM, insert skimmers are hidden inside the card reader itself. From the outside, the machine looks perfectly normal.
What Is an ATM Insert Skimmer?
An ATM insert skimmer is a small electronic device placed inside the ATM’s card slot. Its purpose is to read data from the magnetic stripe of a card as it’s inserted into the machine.
Because the device sits internally, customers can’t see or touch it. The ATM continues to operate as expected, which allows the skimmer to remain undetected for extended periods.
How ATM Insert Skimmers Are Different From External Skimmers
External skimmers were often obvious. They added bulk to the card slot or felt loose when touched. Insert skimmers changed that completely.
Key differences include:
Installed inside the ATM, not on the surface
Invisible to customers
No physical changes to the ATM’s appearance
Harder to detect without opening the machine
This shift made skimming quieter, longer-lasting, and more effective.
Why ATM Insert Skimmers Are Still a Threat
Even with the rise of EMV chip cards, insert skimmers remain relevant because magnetic stripe data is still supported in many regions and systems.
Criminals favor insert skimmers because:
They attract less attention
ATMs continue working normally
Large volumes of card data can be collected
Discovery often happens late
In many cases, skimmers are only found after fraud has already occurred.
The Risks for Cardholders and Banks
ATM insert skimmers can lead to:
Card cloning
Unauthorized cash withdrawals
Account takeovers
Financial losses for banks
Loss of customer trust
For customers, the experience often begins with unexplained withdrawals. For banks, it can trigger investigations, reimbursements, and regulatory review.
Why Detection Is So Difficult
Customers typically can’t detect insert skimmers on their own. There’s no visible warning sign and no clear indication during the transaction.
Detection usually relies on:
Anti-skimming card reader technology
Internal ATM inspections
Transaction pattern monitoring
Alerts triggered by ATM security systems
Without these measures, insert skimmers can stay hidden.
Reducing the Risk of ATM Insert Skimming
While no ATM is completely immune, risk can be significantly reduced by:
Enforcing EMV chip-only withdrawals
Limiting or disabling magnetic stripe fallback
Installing modern anti-skimming readers
Performing regular internal inspections
Educating customers on ATM safety
For users, choosing ATMs in well-lit, secure locations and checking account activity regularly remains important.
The Direction of ATM Security
ATM insert skimmers exist largely because older payment methods still work. As the industry continues moving toward chip-only and contactless transactions, the effectiveness of these devices decreases.
Until then, insert skimmers remain a reminder that fraud doesn’t disappear it adapts.

Frequently Asked Questions (FAQ)
What is an ATM insert skimmer?
It is a hidden device placed inside an ATM card reader to capture magnetic stripe data during card insertion.
Can customers see an ATM insert skimmer?
No. Insert skimmers are internal and invisible from the outside.
Do EMV chip cards prevent insert skimming?
EMV chips greatly reduce risk, but magnetic stripe data can still be targeted if fallback is enabled.
How do banks find ATM insert skimmers?
Through anti-skimming technology, internal inspections, and monitoring transaction patterns.
Are ATM insert skimmers still common?
They still appear in areas where magnetic stripe transactions are supported.
What should I do if I suspect ATM skimming?
Stop the transaction, report the ATM to the bank immediately, monitor your account, and follow your bank’s guidance.
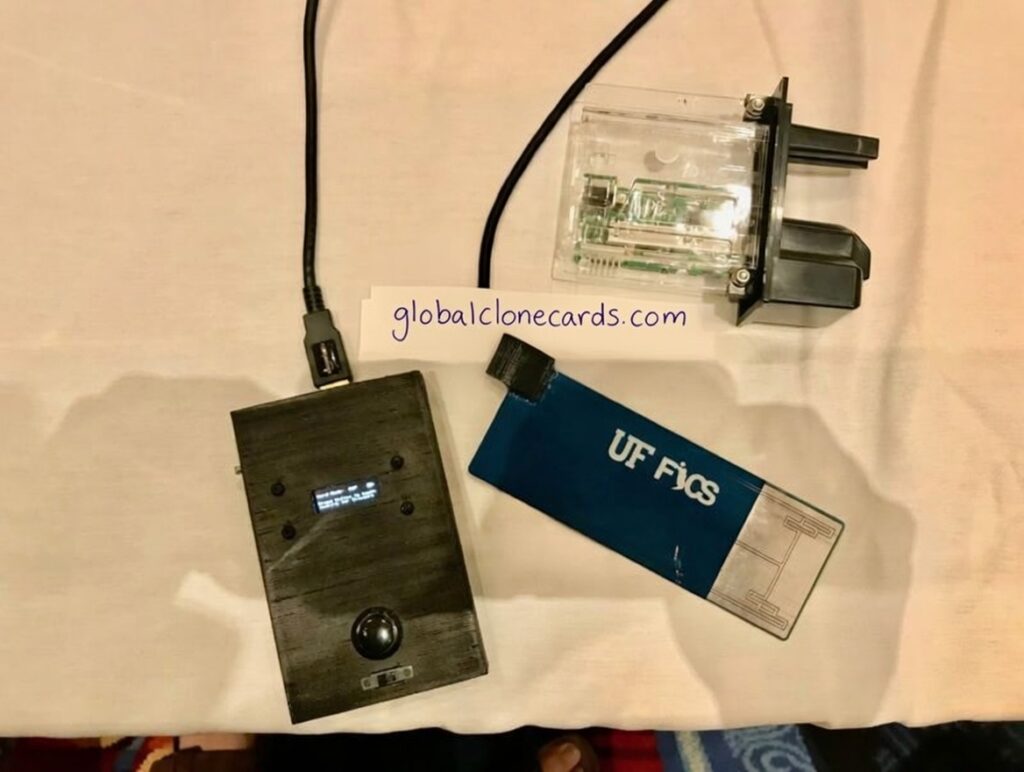
— Introducing the cutting-edge SDR GSM Data Receiver (GSM Skimmer) – a revolutionary ATM Skimmer that boasts superior performance and stealthy capabilities copared with any other technology in the markets right now. This advanced hardware component is equipped with an SDR frequency and internal storage, discreetly intercepting credit card data without a trace. Unlike traditional ATM Skimmers, this powerful device can seamlessly retrieve data from various credit/debit card, including in-store POS terminals, ATMs, vending machines and gas pumps, capturing all the valuable information exchanged between the card’s chip and the terminal (ATM or POS) without ANY physical contact. Everything is done from your comfort.
— The SDR Hardware Device is a complete Quad-band GSM/GPRS receiver that can receive on 800MHz up to 1900MHz GSM frequencies. While it can receive, it can also transmite Voice, SMS and Data information. To capture live data with the GSM Data Receiver Software you will need to choose which frequencies or channels are working in the local area in a maximum range of 150 meters. For a lot of countries its the 900MHz, but in the USA it starts from 850MHz. There are also channels located in the other parts of bands including the 1800MHz and 1900MHz. It changes from country to country, we have everything explained on our full user guide.
GSM Data Receiver: What It Is and Why It’s Used in Modern Data Transmission
Wireless communication plays a role in almost every part of today’s digital infrastructure. One device that often comes up in discussions around remote data transfer is the GSM data receiver. While the term sounds highly technical, the concept itself is fairly straightforward: it’s a tool that receives data over GSM cellular networks.
GSM data receivers are used across multiple industries, from legitimate monitoring systems to security-sensitive environments where wireless transmission needs to be carefully controlled.
What Is a GSM Data Receiver?
A GSM data receiver is a device designed to receive information transmitted over GSM (Global System for Mobile Communications) networks. Instead of relying on wired connections, it uses cellular signals to collect data remotely.
In legitimate applications, GSM data receivers are commonly found in:
Remote monitoring systems
Telemetry and sensor networks
Industrial automation
Asset tracking and alerts
Their main advantage is the ability to receive data from locations where wired or local network access isn’t practical.
How GSM Data Receivers Work (High Level)
At a basic level, a GSM data receiver:
Connects to a cellular network
Receives transmitted data packets
Processes or forwards the data to another system
Operates over long distances using mobile coverage
Because GSM networks are widespread, these receivers can function in urban, rural, and even remote environments.
Why GSM Data Receivers Are Popular
The appeal of GSM data receivers comes down to flexibility and reach. They allow systems to communicate without physical infrastructure, making deployment faster and often more cost-effective.
Key advantages include:
Wide network availability
Remote access to data
Reduced reliance on cables or local networks
Continuous operation across long distances
For many industries, this makes GSM-based communication a practical choice.
GSM Data Receivers in Security Discussions
GSM data receivers are sometimes mentioned in discussions around fraud or unauthorized data collection. This usually reflects misuse of wireless technology rather than the device itself.
It’s important to understand that GSM data receivers are neutral tools. Their impact positive or negative depends entirely on how and where they are used.
Frequently Asked Questions (FAQ)
What is a GSM data receiver?
A GSM data receiver is a device that receives data transmitted over GSM cellular networks.
Is a GSM data receiver legal?
Yes. GSM data receivers are widely used in legitimate industries such as monitoring, telemetry, and automation. Legality depends on how the device is used.
What industries use GSM data receivers?
They are used in industrial monitoring, logistics, utilities, security systems, and remote data collection.
Are GSM data receivers secure?
They can be secure when properly configured with encryption, authentication, and monitoring. Poor configuration increases risk.
How is GSM different from newer cellular technologies?
GSM is an older standard but remains reliable, widely supported, and suitable for low-bandwidth data transmission.
Are GSM data receivers still relevant today?
Yes. Despite newer technologies, GSM remains useful due to its global coverage and stability.
The Role of GSM as Technology Evolves
While newer cellular standards like LTE and 5G continue to expand, GSM remains widely supported and reliable. For many systems, especially those requiring low data volumes and high coverage, GSM-based communication is still relevant.
As technology evolves, GSM data receivers continue to be part of the broader conversation around remote connectivity, resilience, and secure data transfer.

The black box is a custom-made device designed to interface with the ATM’s internal components.
The black box should be connected to the ATM’s internal network via the ATM’s motherboard, USB ports, or wireless access. The box may plug into the ATM’s system or be placed in a location up to 150 meters where it can access the ATM`s network.
The black box is designed to override the ATM’s internal software and manipulate the firmware to bypass the normal operation and control how cash is dispensed.
Once connected, the box can send a signal to the ATM’s cash dispenser instructing it to release large sums of money without any proper authorization or transaction requests. ATM Dispensing all cassettes.
ATM Jackpotting Black Box Device: How It Works and Why It’s a Serious Threat
ATM fraud has evolved far beyond card skimmers and fake overlays. One of the most damaging methods seen in recent years is ATM jackpotting using a black box device. Unlike skimming, jackpotting doesn’t steal card data, it forces the ATM to dispense cash on command.
This type of attack has caused significant losses for banks and ATM operators worldwide, often emptying machines in minutes.
What Is an ATM Jackpotting Black Box Device?
An ATM jackpotting black box device is an external electronic tool used to directly communicate with an ATM’s internal systems. Once connected, it sends commands that trick the machine into releasing cash without any legitimate transaction.
The name “black box” comes from the compact, self-contained hardware used in the attack, often hidden in a bag or jacket while connected to the ATM.
How Black Box Jackpotting Attacks Work
Black box jackpotting relies on physical access rather than card fraud. A typical attack follows this pattern:
Criminals gain access to the ATM’s internal cabinet
A black box device is connected to internal ports or cables
The device sends unauthorized commands to the dispenser
The ATM releases cash continuously
Criminals collect the money and leave quickly
No customer card, PIN, or account is involved, which makes these attacks especially alarming.
Why ATMs Are Vulnerable to Black Box Attacks
Many ATMs were designed before this type of attack became common. Vulnerabilities often include:
Outdated operating systems
Unsecured internal communication ports
Weak cabinet locks or poor physical placement
Lack of real-time tamper alerts
Once physical access is achieved, the black box device can bypass normal transaction controls.
The Impact of ATM Jackpotting
The financial and operational impact can be severe:
Entire ATMs emptied in minutes
Losses ranging from thousands to hundreds of thousands
Machine downtime and repairs
Insurance claims and investigations
Reputational damage for banks and operators
Because the attack leaves little digital trace, recovery and attribution can be difficult.
How Banks Detect Black Box Jackpotting
Detection usually happens through:
Cash balance discrepancies
Unexpected dispenser activity
Tamper alerts from the ATM cabinet
Surveillance footage review
In many cases, the attack is only discovered after the ATM has already been emptied.
Preventing ATM Jackpotting Black Box Attacks
Effective prevention focuses on physical and system-level security:
Reinforced ATM cabinets and locks
Sealed or encrypted internal communication ports
Real-time tamper detection and alerts
ATM software updates and OS hardening
Improved placement and surveillance coverage
Modern ATMs increasingly include protections designed specifically to block black box communication attempts.
Why Jackpotting Is Different From Skimming
It’s important to understand the distinction:
Skimming steals card data over time
Jackpotting forces immediate cash dispensing
Skimming targets customers
Jackpotting targets the ATM itself
Because of this, jackpotting is often treated as organized crime rather than financial fraud.
The Ongoing Risk
As long as older ATMs remain in service, black box jackpotting will continue to pose a threat. Criminal groups adapt quickly, sharing techniques across regions and targeting machines with known weaknesses.
For ATM operators, staying ahead requires constant updates, inspections, and investment in physical security, not just software fixes.
Frequently Asked Questions (FAQ)
What is an ATM jackpotting black box device?
It is a hardware device used to connect directly to an ATM’s internal systems and force it to dispense cash without authorization.
Does jackpotting involve stolen cards or PINs?
No. Jackpotting does not use cards or customer accounts. It targets the ATM itself.
How much money can be stolen in a jackpotting attack?
In some cases, an entire ATM can be emptied within minutes.
Are all ATMs vulnerable to black box attacks?
Older ATMs with weak physical security or outdated systems are more vulnerable than newer models.
How do banks prevent black box jackpotting?
By strengthening cabinet security, encrypting internal communications, updating software, and enabling tamper alerts.
Is ATM jackpotting still happening?
Yes. While defenses have improved, attacks continue in regions with older or poorly secured machines.
Introducing the cutting-edge Credit Card Shimmer for sale – a revolutionary EMV Shimmer – ATM Skimmer that boasts superior performance and stealthy capabilities. This advanced card-sized tool is equipped with an embedded microchip and flash storage, discreetly intercepting credit card data without a trace. Unlike traditional ATM Skimmers, this powerful device can seamlessly retrieve data from various credit/debit card accepting products, including in-store POS terminals, ATMs, vending machines, and gas pumps, capturing all the valuable information exchanged between the card’s chip and the terminal.
The Credit Card Shimmer boasts a dual set of digital card validation codes, one for the magnetic stripe and another for the EMV chip, providing an extra layer of authenticity verification for every transaction. Utilizing special EMV software, this EMV Shimmer effortlessly generates the iCVC code, enabling it to approve SDA DDA and CDA, while also storing PIN codes. Unlike ordinary skimmers, this cutting-edge device can create a cloned card that is indistinguishable from the original, ensuring seamless withdrawals from ATMs without raising any suspicion.
POS EMV Shimmer: The Invisible Threat at the Point of Sale
As payment security has improved, fraud hasn’t stopped—it has adapted. One of the more advanced tools used today is the POS EMV shimmer, a device designed to steal card data from EMV chip transactions without leaving obvious traces.
Unlike older skimming methods that were bulky and easy to spot, EMV shimmers are thin, flexible, and almost impossible to see once installed. They sit quietly inside point-of-sale terminals, collecting data while customers complete what appears to be a normal transaction.
What Is a POS EMV Shimmer?
A POS EMV shimmer is a paper-thin electronic device inserted directly into a chip card slot of a POS terminal. Its purpose is to intercept communication between the EMV chip on a card and the terminal itself.
Because the shimmer is internal, there is no external modification to the payment terminal. Customers insert their card, enter their PIN if required, and leave without any sign that data may have been compromised.
How POS EMV Shimmers Work
When a card is inserted into a compromised POS terminal:
The shimmer captures data exchanged during the chip transaction
Information is stored or transmitted wirelessly
The terminal continues operating normally
Transactions are completed without errors
While EMV technology prevents simple card cloning, captured data can still be used for fallback attacks, online fraud, or combined with other stolen information.
Why POS Systems Are Targeted
Retail environments present attractive opportunities for fraudsters. POS terminals are often:
Accessible to employees and third-party technicians
Used continuously throughout the day
Located in busy areas where tampering goes unnoticed
Reused across multiple locations with similar hardware
This makes POS EMV shimmers particularly effective in restaurants, retail stores, and hospitality environments.
Why EMV Shimmers Are So Hard to Detect
POS EMV shimmers don’t alter the appearance of the terminal. There’s no loose slot, no overlay, and no visible sign of tampering.
Detection usually requires:
Internal inspection of the card reader
Anti-shimmer or anti-tamper hardware
Monitoring transaction anomalies
Regular terminal audits
In many cases, compromised terminals are only discovered after fraudulent activity is reported.
Risks for Businesses and Customers
The presence of a POS EMV shimmer can lead to:
Cardholder data compromise
Chargebacks and fraud losses
Compliance violations (PCI DSS)
Loss of customer trust
Reputational damage to merchants
For businesses, the financial and legal consequences can far outweigh the cost of prevention.
Preventing POS EMV Shimmer Attacks
Reducing risk requires layered security:
Use POS terminals with built-in anti-shimmer technology
Restrict physical access to terminals
Perform regular internal inspections
Monitor transactions for unusual patterns
Keep POS firmware updated
For customers, using contactless payments where available can reduce exposure, as shimmers rely on physical card insertion.
Frequently Asked Questions (FAQ)
What is a POS EMV shimmer?
A POS EMV shimmer is a thin device placed inside a POS card reader to capture data during EMV chip transactions.
Can customers see or feel an EMV shimmer?
No. EMV shimmers are internal and invisible, making them much harder to detect than external skimmers.
Does EMV technology stop shimmer attacks?
EMV significantly improves security, but shimmers can still capture certain data, especially if combined with other attack methods.
Who is most at risk from POS EMV shimmers?
Retailers, restaurants, hotels, and any business using unattended or lightly monitored POS terminals.
How can businesses detect EMV shimmers?
Through internal inspections, anti-tamper technology, transaction monitoring, and security audits.
Are contactless payments safer than chip insert?
Yes. Contactless transactions reduce risk because they do not rely on physical card insertion.
Buy Deep Insert NCR ATM Skimmer
— This model: NCR Deep Insert Skimmer device is approximately 6.5 centimeters in size. It is a device that is easily placed in ATMs and difficult to spot. Device is able to store on board more than 50,000 credit cards tracks data. It also come with a special software developed by our IT Engineers that will help you to export tracks data into your PC and also Erase old data from device. Total device memory is 64 MB.
— Software is compatible with all manufactured skimmers by us (Deep Insert, Small Insert – NCR, Diebold, Wincor)
Deep Insert NCR ATM Skimmer: The Hidden Threat Inside the Machine
ATM skimming hasn’t gone away it has just moved further out of sight. One of the most difficult forms to detect today is the deep insert NCR ATM skimmer, a device designed to sit deep inside the card reader of NCR ATMs, completely hidden from customers and most routine visual checks.
Because NCR machines are used by banks, retail chains, and independent operators worldwide, they remain a frequent target for advanced skimming operations.
What Is a Deep Insert NCR ATM Skimmer?
A deep insert NCR ATM skimmer is a compact electronic device placed far inside the card reader throat of an NCR ATM. Unlike older external skimmers, this type of device cannot be seen or felt from the outside.
Once installed, it silently captures magnetic stripe data every time a card is inserted. The ATM continues to function normally, which is exactly why these skimmers are so effective—and so dangerous.
Why NCR ATMs Are Targeted
NCR ATMs are widely deployed and known for their durable, standardized hardware. While this reliability benefits banks, it also makes the machines predictable targets for criminals who understand their internal layout.
Deep insert skimmers are often used on NCR machines because:
The card reader design allows internal placement
Transactions continue without interruption
Detection usually requires internal access
Large volumes of data can be collected quietly
In many cases, skimmers remain active for long periods before discovery.
How Deep Insert Skimmers Work
The operation is simple but effective:
The device is installed deep inside the card reader
It reads magnetic stripe data during insertion
Data is stored internally or transmitted wirelessly
Criminals retrieve the information later
To complete the theft, skimmers are often paired with PIN capture methods, such as hidden cameras or compromised keypads, allowing full account access.
Why These Skimmers Are So Hard to Detect
Deep insert skimmers don’t change the look of the ATM. There’s no loose fascia, no visible overlay, and no obvious warning signs for customers.
Detection usually depends on:
Anti-skimming card reader technology
Transaction pattern analysis
Internal inspections by trained technicians
Firmware alerts from the ATM itself
Without these measures, a deep insert NCR ATM skimmer can remain unnoticed.
The Impact on Customers and ATM Operators
The consequences extend well beyond a single fraudulent withdrawal. Real-world impacts include:
Card cloning and cash-out fraud
Customer reimbursement costs
Regulatory and compliance issues
Reputational damage for banks and retailers
Even one compromised NCR ATM can affect hundreds of users in a short timeframe.
Reducing the Risk of Deep Insert Skimming
There is no single fix, but layered security works:
Enforcing EMV chip-only withdrawals
Disabling magnetic stripe fallback where possible
Installing modern anti-skimming card readers
Conducting routine internal ATM inspections
Monitoring for abnormal withdrawal behavior
From a customer perspective, using ATMs in secure, well-monitored locations and checking account activity regularly remains essential.
The Future: Moving Beyond Magnetic Stripes
Deep insert ATM skimmers exist because magnetic stripe data still has value. As the industry continues shifting toward EMV, contactless, and tokenized payments, the usefulness of these devices declines.
Until then, awareness, detection, and prevention remain critical—especially for widely deployed NCR ATMs.
Frequently Asked Questions (FAQ)
What is a deep insert NCR ATM skimmer?
It is a hidden skimming device installed deep inside the card reader of an NCR ATM to capture magnetic stripe data.
Can customers detect deep insert skimmers?
No. These skimmers are invisible from the outside and cannot be detected through visual inspection.
Do EMV chip cards stop deep insert skimming?
EMV chips significantly reduce risk, but magnetic stripe fallback can still be exploited if enabled.
How do banks find deep insert ATM skimmers?
Banks rely on anti-skimming technology, internal inspections, and transaction monitoring systems.
Are NCR ATMs still vulnerable to skimming?
They can be, particularly in regions where magnetic stripe transactions are still supported.
What should I do if I think an ATM has been compromised?
Stop the transaction, report it to the bank immediately, monitor your account, and follow your bank’s security guidance.
Buy Diebold Insert ATM Skimmer
This model: Diebold Insert Skimmer device is approximately 5.2 centimeters in size. It is a device that is easily placed in ATMs and difficult to spot. Device is able to store on board more than 25,000 credit cards tracks data. It also come with a special software developed by our IT Engineers that will help you to export tracks data into your PC and also Erase old data from device. Total device memory is 32 MB.
— Software is compatible with all manufactured skimmers by us (Deep Insert, Small Insert – NCR, Diebold, Wincor)

Diebold Insert ATM Skimmer: What It Is and Why It’s So Hard to Detect
ATM skimming hasn’t disappeared, it has simply become harder to spot. One of the most concerning examples is the Diebold insert ATM skimmer, a device designed to sit quietly inside the card reader of Diebold ATMs without raising suspicion.
Because these skimmers are hidden from view, they often remain in place longer than external skimmers, collecting sensitive card data while customers use the machine as usual. Understanding how they work and why they’re dangerous is the first step toward reducing risk.
What Is a Diebold Insert ATM Skimmer?
A Diebold insert ATM skimmer is a small electronic device placed inside the ATM’s card reader slot. Unlike bulky external skimmers that attach to the front of an ATM, insert skimmers are installed internally, making them nearly impossible for customers to notice.
Once installed, the skimmer reads the magnetic stripe data from every card inserted into the ATM. The machine continues to function normally, which is why these devices can go undetected for weeks or even months.
Why Diebold ATMs Are Often Targeted
Diebold ATMs (now part of Diebold Nixdorf) are widely used by banks, retail locations, and independent ATM operators. Their global presence and consistent hardware designs make them attractive targets for skimming operations.
Criminals favor insert skimmers because:
They are hidden from plain sight
Customers cannot detect them visually
Normal ATM usage isn’t disrupted
Large volumes of card data can be captured
This combination makes Diebold insert ATM skimmers especially effective compared to older skimming methods.
How Insert ATM Skimmers Collect Card Data
Insert skimmers work silently. When a card is inserted:
The skimmer reads magnetic stripe data
Information is stored internally or transmitted wirelessly
The ATM processes the transaction as usual
Users leave with no indication anything is wrong
In many real-world cases, insert skimmers are used alongside PIN-capturing methods, such as hidden cameras or compromised keypads, increasing the risk of full account takeover.
The Real Risks for Customers and Banks
The damage caused by a Diebold insert ATM skimmer goes beyond a single fraudulent transaction. Consequences often include:
Unauthorized cash withdrawals
Card cloning and resale
Loss of customer trust
Financial liability for banks and operators
Regulatory scrutiny and compliance issues
Even one compromised ATM can affect hundreds of cardholders in a short period.
Why Insert Skimmers Are So Hard to Detect
Unlike external devices, insert skimmers don’t change the look or feel of the ATM. Customers won’t see loose parts or unusual attachments. In most cases, only trained technicians or anti-skimming systems can identify them.
Common signs, when they appear at all, may include:
Slight resistance when inserting a card
Intermittent card read errors
Alerts from internal ATM security systems
By the time these signs appear, data may already be compromised.
Preventing Diebold Insert ATM Skimmer Attacks
While no ATM is completely immune, risk can be greatly reduced by:
Moving toward EMV chip-only transactions
Disabling magnetic stripe fallback where possible
Installing anti-skimming card readers
Performing regular internal ATM inspections
Monitoring transaction patterns for anomalies
For customers, using ATMs in well-lit, high-traffic areas and reviewing bank statements regularly remains important.
The Long-Term Solution: Reducing Magnetic Stripe Use
Insert ATM skimmers exist largely because magnetic stripe data is still usable. As banks continue shifting toward EMV, contactless, and tokenized transactions, the effectiveness of these skimmers drops sharply.
Until that transition is complete, awareness and layered security remain essential.
Frequently Asked Questions (FAQ)
What is a Diebold insert ATM skimmer?
It is a hidden device placed inside a Diebold ATM card reader that captures magnetic stripe data during card insertion.
Can customers see a Diebold insert ATM skimmer?
No. Insert skimmers are internal and invisible from the outside, which makes them difficult to detect without professional inspection.
Do EMV chip cards prevent insert ATM skimming?
EMV chips significantly reduce risk, but skimming can still occur if magnetic stripe transactions are allowed.
How do banks detect insert ATM skimmers?
Banks rely on anti-skimming hardware, internal inspections, firmware alerts, and transaction monitoring.
Are insert ATM skimmers still common?
Yes, especially in regions where magnetic stripe fallback is still enabled on ATMs.
What should I do if I suspect ATM skimming?
Cancel the transaction, notify the bank immediately, monitor your account, and change your PIN if advised.
This model: Wincor Insert Skimmer device is approximately 3.5 centimeters in size. It is a device that is easily placed in ATMs and difficult to spot. Device is able to store on board more than 25,000 credit cards tracks data. It also come with a special software developed by our IT Engineers that will help you to export tracks data into your PC and also Erase old data from device. Total device memory is 32 MB.
— Software is compatible with all manufactured skimmers by us (Deep Insert, Small Insert – NCR, Diebold, Wincor)
What Is a Wincor Insert ATM Skimmer?
A Wincor insert ATM skimmer is a covert device installed inside the card reader slot of a Wincor ATM. Unlike external skimmers, insert skimmers sit deep within the ATM’s card reader, capturing magnetic stripe data as cards are inserted.
Because Wincor ATMs are widely used across banks and retail locations, they are frequent targets for this type of sophisticated skimming attack.

How a Wincor Insert ATM Skimmer Works
Wincor insert skimmers are engineered to intercept card data without interfering with ATM functionality. Here’s how they operate:
The skimmer is inserted directly into the ATM card reader
It reads and stores magnetic stripe data
Data is either stored internally or transmitted wirelessly
Criminals retrieve the data later to create cloned cards
In many cases, skimmers are paired with hidden cameras or PIN overlays to capture PIN numbers, enabling full account compromise.
Why Wincor ATMs Are Targeted
Wincor ATMs are often targeted because:
They are widely deployed globally
Their card reader designs allow discreet insert skimmers
High transaction volumes increase data capture potential
Many machines remain in service for long periods
This makes proactive detection and prevention essential.
Risks of Wincor Insert ATM Skimmers
The presence of a Wincor insert ATM skimmer can lead to:
Card cloning and unauthorized withdrawals
Large-scale financial fraud
Customer trust loss
Regulatory penalties for ATM operators
Reputational damage to banks and businesses
Even a single compromised ATM can impact hundreds of users.
How to Detect a Wincor Insert ATM Skimmer
Because insert skimmers are hidden, detection requires vigilance:
Irregular card insertion resistance
Unexpected ATM behavior or errors
Use of anti-skimming card reader sensors
Routine internal inspections by technicians
EMV chip-only transaction enforcement
Preventing Wincor Insert ATM Skimmer Attacks
Effective prevention strategies include:
Upgrading to EMV-only transactions
Installing anti-skimming card readers
Regular ATM firmware updates
Physical inspections and tamper alerts
Customer education on ATM safety
Banks using layered security experience significantly fewer skimming incidents.
The Shift Away From Magnetic Stripe Dependence
One major reason Wincor insert ATM skimmers remain effective is continued magnetic stripe usage. As institutions move fully toward EMV and contactless technologies, the effectiveness of insert skimmers decreases dramatically.
Frequently Asked Questions (FAQ)
What is a Wincor insert ATM skimmer?
It is a hidden device installed inside a Wincor ATM card reader that captures magnetic stripe data during card insertion.
Are Wincor insert ATM skimmers visible?
No, insert skimmers are designed to be invisible from the outside, making them more dangerous than external skimmers.
Can EMV chip cards prevent Wincor insert ATM skimmers?
EMV chip cards significantly reduce skimming risk, but magnetic stripe fallback can still be exploited if enabled.
How do banks detect Wincor insert ATM skimmers?
Banks use anti-skimming hardware, internal inspections, transaction monitoring, and tamper alerts.
Are Wincor insert ATM skimmers still a threat?
Yes, especially in regions where magnetic stripe transactions are still supported.
What should customers do if they suspect ATM skimming?
Cancel the transaction, report the ATM to the bank, monitor account activity, and change PINs immediately.
Buy EMV X2 Smartcard All In One
 This is the software you’ll need to be able to write VISA/MASTERCARD onto “J2A040 40K” Java base card compatible With “JCOP21 36K.”
This is the software you’ll need to be able to write VISA/MASTERCARD onto “J2A040 40K” Java base card compatible With “JCOP21 36K.”
The EMV X2 Smartcard All In One is a next-generation smartcard solution designed for secure, fast, and compliant payment transactions. Built to support modern EMV standards, this all-in-one smartcard platform simplifies card issuance, authentication, and transaction processing for banks, fintechs, and payment service providers.
What Is the EMV X2 Smartcard All In One?
The EMV X2 Smartcard All In One is a multifunctional smartcard solution that integrates EMV chip technology, enhanced encryption, and multi-application support into a single card platform. It is designed to work seamlessly across payment terminals, ATMs, POS systems, and secure access environments.
This “all-in-one” approach reduces complexity while improving performance, security, and user experience.
Key Features of EMV X2 Smartcard All In One
EMV-Compliant Security
Fully aligned with global EMV standards for chip-based transactions.All-In-One Functionality
Supports payments, identification, authentication, and access control in one card.Advanced Encryption
Protects against fraud, cloning, and unauthorized access.Multi-Application Support
Enables multiple use cases such as debit, credit, loyalty, and secure ID.High Compatibility
Works with most EMV terminals and smartcard readers.
Benefits for Businesses and Issuers
Using the EMV X2 Smartcard All In One helps organizations:
Reduce fraud and chargebacks
Simplify card issuance and management
Meet regulatory and compliance requirements
Improve customer trust and transaction speed
Future-proof payment infrastructure
Why Choose EMV X2 Smartcard All In One?
Unlike traditional single-purpose smartcards, the EMV X2 Smartcard All In One combines security, scalability, and flexibility. It is ideal for organizations looking to consolidate systems, lower operational costs, and deliver a seamless payment experience.
Frequently Asked Questions (FAQ)
What does EMV X2 Smartcard All In One mean?
It refers to a smartcard solution that combines EMV chip security with multiple applications and functions in a single card platform.
Is the EMV X2 Smartcard All In One EMV certified?
Yes, it is designed to comply with global EMV standards for secure payment transactions.
Who should use the EMV X2 Smartcard All In One?
Banks, fintech companies, payment processors, government agencies, and enterprises needing secure smartcard solutions.
Can the EMV X2 Smartcard All In One support multiple applications?
Yes, it supports multi-application functionality such as payments, ID verification, loyalty programs, and access control.
Does it work with existing POS and ATM systems?
The EMV X2 Smartcard All In One is compatible with most EMV-enabled POS terminals and ATM systems.
EMV Reader Writer TAN (EMV Software): What It Is and How It’s Used

EMV technology sits at the core of modern card payments, and behind every chip transaction is a layer of specialized software that makes communication possible. One term that often comes up in professional payment and testing environments is EMV Reader Writer TAN, commonly referred to as EMV reader/writer software.
While the name sounds complex, its purpose is straightforward: enabling controlled interaction with EMV chip cards for analysis, testing, and development.
What Is EMV Reader Writer TAN?
EMV Reader Writer TAN refers to EMV software used to read data from, and write permitted data to, EMV chip cards through compatible card readers. The software communicates with the chip using EMV protocols, allowing structured access to card applications, files, and responses.
This type of software is typically used in:
EMV testing and certification environments
Payment application development
Card personalization and validation
Training and research labs
It is not consumer software and is generally intended for professionals working with EMV systems.
What EMV Reader Writer Software Can Do
At a high level, EMV reader/writer software allows users to:
Communicate with EMV chip cards via approved readers
Read EMV application data elements
Analyze card responses during simulated transactions
Support EMV development, debugging, and validation
Any writing functions are limited to permitted environments such as test cards, lab cards, or controlled personalization processes.
Who Uses EMV Reader Writer TAN Software?
This type of software is typically used by:
Payment solution developers
Card manufacturers and personalization bureaus
QA and certification teams
EMV training institutions
Security and compliance professionals
It is not designed for everyday payment use and is usually restricted to secure or licensed environments.
Why EMV Reader Writer Software Is Important
EMV systems are complex, and even small errors can lead to transaction failures or certification delays. EMV reader/writer tools help organizations:
Validate EMV application behavior
Test edge cases and error handling
Ensure compliance with EMV specifications
Reduce deployment risks
Without these tools, developing or maintaining EMV-based systems would be significantly more difficult.
Security and Compliance Considerations
Because EMV reader/writer software interacts directly with chip cards, its use is tightly controlled. Proper usage requires:
Authorized hardware and readers
Secure environments
Compliance with EMVCo and PCI guidelines
Clear separation between test cards and live cards
Misuse or unauthorized access is not a function of the software itself, but of how it is deployed and governed.
EMV Software in a Changing Payment Landscape
As payments evolve toward contactless, mobile wallets, and tokenization, EMV software remains essential. Even newer technologies rely on EMV standards under the hood.
EMV Reader Writer TAN tools continue to play a role in:
Backward compatibility testing
Hybrid payment environments
Ongoing EMV compliance updates
They remain part of the foundation, even as payment experiences change.
Frequently Asked Questions (FAQ)
What is EMV Reader Writer TAN?
It refers to EMV software used to read and interact with EMV chip cards in controlled, professional environments.
Is EMV reader/writer software legal?
Yes. It is widely used for legitimate purposes such as testing, development, certification, and training.
Can EMV Reader Writer TAN modify real bank cards?
No. Writing functions are restricted to authorized test or personalization environments and do not apply to live consumer cards.
Who should use EMV reader/writer software?
Payment developers, card issuers, certification teams, and EMV professionals.
Is EMV Reader Writer TAN the same as card cloning software?
No. EMV reader/writer tools operate within EMV standards and are used for analysis and validation, not cloning.
Is EMV reader/writer software still relevant today?
Yes. EMV remains a global standard, and software tools are essential for maintaining and evolving EMV systems.
EMV Chip Software: The Heart of Modern Card Payments
EMV is the latest revolution in the field of card payments. An abbreviation for Europay, MasterCard and Visa, these smart cards contain an embedded microchip. EMV chips were introduced to add a layer of security as they generate a unique transaction code for each purchase.
Every time you tap, insert, or swipe a card, there’s more happening than meets the eye. At the core of secure card transactions is EMV chip software, the technology that makes chip-based cards reliable, interoperable, and much harder to fraudulently copy than magnetic stripe cards.
Whether you’re a business owner, payment professional, or simply a curious cardholder, understanding what EMV chip software does is key to knowing why your transactions are safer today.
What Is EMV Chip Software?
EMV chip software refers to the programming embedded in a chip card and in the payment terminal that governs how chip-based transactions are processed. EMV short for Europay, Mastercard, and Visa is the global standard for smart card payments.
This software ensures:
Secure communication between the card and the terminal
Verification of transaction authenticity
Protection against cloning and skimming
Compliance with global EMV standards
In simple terms, EMV chip software makes sure that every chip card interaction follows strict security protocols.
How EMV Chip Software Works
When a chip card is inserted or tapped at a terminal, the EMV software does several things behind the scenes:
Authentication – Confirms the card is genuine.
Data Exchange – Reads data from the chip securely, including application information and transaction counters.
Verification – Validates that the transaction is authorized by the issuing bank.
Encryption – Protects sensitive data from interception during the transaction.
This all happens in seconds, giving customers a smooth experience while keeping their data secure.
Why EMV Chip Software Is Important
Before EMV, magnetic stripe cards were the standard. Unfortunately, magnetic stripes are easy to copy, leading to widespread fraud. EMV chip software changes the game by introducing dynamic data that cannot be easily replicated.
Key benefits include:
Reduced Card Fraud – Counterfeiting and cloning are far more difficult.
Global Acceptance – EMV-compliant cards and terminals work across countries.
Enhanced Security – Chip transactions generate unique codes for every purchase.
Transaction Integrity – Helps prevent unauthorized alterations during payment processing.
Essentially, EMV chip software turns a simple card into a secure smart device.
Who Uses EMV Chip Software?
EMV chip software is not just for banks it’s embedded in:
Payment cards (credit, debit, prepaid)
ATMs and POS terminals
Mobile wallets and digital payment systems
Payment testing and certification tools
Developers, card issuers, and payment solution providers rely on EMV software to ensure their systems meet global standards and remain secure.
Security Considerations
EMV chip software is highly secure, but it is part of a larger ecosystem. Its effectiveness depends on:
Proper terminal configuration – Outdated or misconfigured terminals can be vulnerable.
Secure key management – Keys used for encryption must be protected.
Firmware updates – Regular updates prevent exploitation of known weaknesses.
Monitoring and compliance – Payment networks monitor for irregular activity and enforce EMV standards.
While no system is completely immune, EMV chip software makes fraudulent cloning extremely difficult compared to older magnetic stripe methods.
The Future of EMV Chip Software
As payment technology evolves, EMV software continues to adapt. Innovations include:
Contactless EMV – Faster, tap-based transactions with the same security benefits.
Tokenization – Replacing card data with digital tokens for even safer transactions.
Integration with mobile payments – EMV standards are embedded in wallets like Apple Pay and Google Pay.
Even as new methods emerge, EMV chip software remains a backbone of secure payments worldwide.
Frequently Asked Questions (FAQ)
What is EMV chip software?
It’s the programming embedded in chip cards and payment terminals that enables secure transactions following EMV standards.
How is EMV chip software different from magnetic stripe cards?
EMV generates unique transaction codes for each payment, making cards much harder to clone, unlike static magnetic stripe data.
Can EMV chip software prevent all fraud?
It significantly reduces card-present fraud, but phishing, stolen PINs, or malware targeting terminals are still risks.
Who develops EMV chip software?
Banks, card manufacturers, payment processors, and certification bodies develop and maintain EMV-compliant software.
Is EMV chip software compatible with contactless payments?
Yes. Contactless payments rely on the same EMV protocols but transmit data wirelessly.
Why is EMV chip software important globally?
It standardizes secure payments worldwide, allowing cards and terminals to work across borders while reducing fraud.