GSM Data Receiver POS/ATM Skimmer – How Modern Card Fraud Works and How to Stay Protected
In an era where digital payments dominate daily life, criminals continuously innovate to exploit vulnerabilities in financial infrastructure. One of the most insidious tools in their arsenal is the GSM data receiver POS/ATM skimmer a compact, cellular-enabled device that captures card information and PINs remotely from ATMs and point-of-sale (POS) terminals. By leveraging GSM (Global System for Mobile Communications) technology, these skimmers transmit stolen data in real time via SMS or data packets, eliminating the need for physical retrieval and drastically reducing the perpetrator’s risk of capture.

These devices target both legacy magnetic stripe systems and, in some adaptations, chip-enabled transactions through fallback attacks or shimming. While EMV chip technology has curtailed some traditional skimming, GSM-equipped skimmers remain effective at high-traffic, less-secured locations like standalone ATMs, gas stations, and retail POS systems. According to U.S. Secret Service advisories from early 2025, skimming crimes continue to cause hundreds of millions in annual losses, with organized groups deploying increasingly sophisticated wireless variants.
This article provides a comprehensive, educational overview of GSM data receiver skimmers, including their hardware, associated software, operational methods, prevalence, legal consequences, and practical defenses. Importantly, any use, possession, or distribution of these devices for fraudulent purposes is a serious federal crime in most
GSM Data Receiver POS/ATM Skimmer
, carrying penalties of years in prison and substantial fines. The goal here is awareness and protection not facilitation.
The GSM data receiver POS/ATM skimmer is one of the most advanced tools used in financial fraud today. While traditional skimmers required physical retrieval, GSM-based skimmers use wireless mobile networks to transmit stolen data instantly. Because of this evolution, criminals can collect information without returning to the compromised machine.
As digital payments increase worldwide, so does the interest of cybercriminals in exploiting vulnerable payment systems. Understanding how these skimmers work is essential for consumers, banks, and merchants who want to protect themselves from costly financial loss.
This article explains the technology, the software, the risks, and the defenses used against GSM skimming.

What Is a GSM Data Receiver POS/ATM Skimmer?
A GSM data receiver POS/ATM skimmer is a hidden electronic device attached to a payment terminal or ATM. Its purpose is to capture card data and PIN information when a customer inserts or swipes their card. The captured information is then transmitted using GSM mobile networks, similar to how a phone sends text messages.
Unlike older skimmers that stored data locally, GSM skimmers send information in real time to remote operators. This makes them harder to detect and much more dangerous.
These devices are often installed inside ATM cabinets or inside POS terminals in stores, where they remain invisible to users.
How GSM Skimming Works in POS and ATM Systems
The skimming process follows a predictable pattern:
First, criminals install a skimmer inside or on a card reader. This device reads the magnetic stripe or chip data when a customer inserts their card.
Second, a small keypad overlay or micro camera records the PIN when the customer types it.
Third, the GSM module inside the skimmer sends all captured data through the mobile network to the attacker.
Finally, the attacker receives the data on a computer or phone and uses it to create cloned cards or commit online fraud.
Because the data is transmitted wirelessly, criminals do not need to revisit the ATM or POS terminal.
Core Components and How GSM Data Receiver Skimmers Function
A typical GSM data receiver skimmer consists of several integrated parts designed for stealth and efficiency:
- Card Data Capture Module — A reader that intercepts magnetic stripe data (Track 1 and Track 2) as the card is swiped or inserted. In POS environments, it often appears as an overlay matching the terminal’s aesthetics.
- PIN Capture Mechanism — Usually a pinhole camera hidden in a brochure holder, bezel, or fake keypad overlay that records keystrokes.
- GSM Transmitter — The defining feature: a cellular modem with SIM card slot, antenna, and battery. It sends captured data instantly via text messages or GPRS to a remote phone or server.
- Storage Backup — Internal memory (often a microSD card) holds thousands of records if transmission fails.
Operation follows a straightforward yet devastating sequence:
- Installation (often under 60 seconds) on a vulnerable ATM or POS terminal.
- Legitimate transaction occurs; skimmer reads card data and records PIN.
- GSM module transmits the full “dump” (card number, expiration, service code, PIN) wirelessly.
- Criminal receives data remotely, clones cards, and exploits accounts.
For POS terminals (common at retail counters, restaurants, or gas pumps), overlays cover the keypad and reader, capturing both swipe data and PIN entry. ATMs often use insert-style skimmers hidden deep in the slot, combined with external cameras.
The GSM advantage is clear: no return visit required. Traditional skimmers forced criminals back to the scene — risking CCTV or patrols. Wireless transmission allows immediate exploitation, even if the device is later discovered.
Visual examples illustrate this design. Here’s a classic GSM skimmer module with visible antenna and SIM slot:
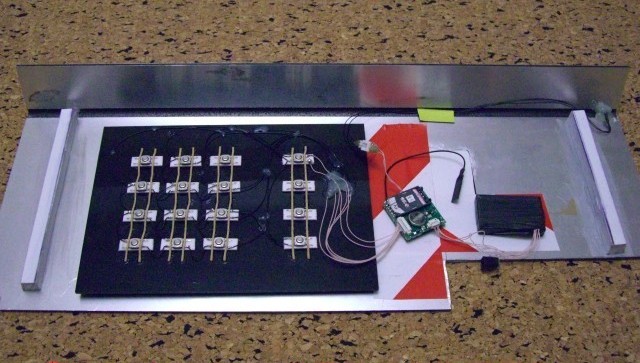
Another shows the backside of a PIN pad overlay integrated with GSM transmission:
These images highlight how discreetly the technology integrates.
The Software Component: Tools for Data Management and Exploitation
While the hardware captures data, companion software turns raw intercepts into usable fraud material. Vendors of these illicit devices often bundle proprietary tools, frequently labeled as “V5.2” or similar versions.
Key software functions include:
- Data Retrieval — Connect the device via USB to a computer; software automatically downloads stored records from internal memory.
- Dump Parsing and Organization — Separates Track 1/Track 2 data, extracts card numbers, expiration dates, CVVs, and PINs.
- Cloning Preparation — Formats data for encoding onto blank magnetic stripe cards using card writers/encoders.
- Transmission Management — Configures GSM settings, SIM details, recipient phone numbers, and encryption (in advanced models).
- EMU/Emulator Features — Some include emulation modes to simulate legitimate readers or test captures.
These tools are not legitimate payment software — they are custom-built for criminal use, often sold on underground forums or shady e-commerce sites. Installation typically involves running executables on Windows machines, with interfaces showing real-time incoming SMS dumps.
Illicit sellers advertise “automatic” collection, claiming capacity for 25,000+ records and instant delivery to the buyer’s PC. In reality, many such packages are scams themselves, delivering malware or non-functional code.
A typical bundled software interface might display incoming card dumps in a dashboard format, though exact screenshots are rarely public due to their criminal nature.
Understanding the Software Behind GSM Skimmers
The software used in GSM data receiver skimmers is designed to control data capture, encryption, and transmission. It runs on small microcontrollers embedded in the device.
This software performs several tasks:
It activates when a card is inserted into the machine.
It records card number, expiration date, and track data.
It waits for PIN input data from a keypad overlay or camera.
It compresses and encrypts the stolen information.
It sends the data through GSM SMS or data connections.
Some advanced versions also allow remote commands, which let criminals reset the device, change phone numbers, or erase memory to avoid detection.
Why GSM Skimmers Are So Dangerous
GSM skimmers are dangerous because they operate silently and remotely. They do not require criminals to return to the crime scene. As a result, the risk of being caught is much lower.
Victims often do not realize their data was stolen until fraudulent transactions appear on their bank statements. By then, the criminals have already used or sold the stolen information.
Businesses also suffer, because banks may fine them for weak security. Customers may also lose trust in a store or ATM brand.
Deployment on POS vs. ATM: Key Differences
ATM Skimming Targets standalone or lobby machines. Insert skimmers hide inside the reader slot; external GSM modules attach nearby. Pinhole cameras in fake bezels or overlays capture PINs. High success in low-surveillance areas.
POS Skimming Common at gas pumps, small retailers, or handheld terminals. Overlays mimic the terminal’s top panel or keypad. GSM allows remote harvesting without swapping entire devices. Some models fake “approved” receipts to avoid suspicion.
Both exploit magnetic stripe fallback when chips fail or aren’t required. Contactless skimming (via NFC/RFID interception) is emerging but less common in pure GSM setups.
An example of a POS overlay skimmer with integrated components:
A hidden camera setup often paired with these skimmers for PIN capture:
Prevalence, Recent Trends, and Enforcement (2025–2026 Perspective)
Skimming persists despite EMV adoption. The U.S. Secret Service’s February 2025 advisory highlighted ongoing threats at pharmacies, gas stations, and grocery stores, with criminals adapting to chip security through overlays and wireless tech.
Recent operations recovered hundreds of devices, preventing millions in losses. Organized rings often international sell data in bulk on dark web markets.
Trends include infrared relays for insert skimmers (bypassing radio detection) and hybrid GSM setups for longer battery life.
Where GSM POS and ATM Skimmers Are Installed
These devices are usually installed in:
Busy ATM locations
Gas station payment pumps
Small retail shops
Unattended kiosks
Public transport ticket machines
Criminals target places with high transaction volume and low supervision. Machines that are not frequently inspected are the easiest targets.
How Banks and Payment Companies Detect GSM Skimmers
Modern financial institutions use advanced detection systems to identify GSM skimming attacks. These systems include:
Radio frequency scanners that detect illegal GSM signals near ATMs
Transaction monitoring software that flags unusual withdrawals
AI-powered fraud detection tools
Tamper detection sensors inside machines
If a GSM skimmer sends data, it creates radio activity. Banks and telecom companies can locate and shut down suspicious signals.
Detection and Warning Signs
- Tug on card readers/keypads — legitimate ones don’t move.
- Look for misalignments, extra bulk, scratches, or unusual stickers.
- Shield PIN entry with your hand to block cameras.
- Avoid standalone ATMs; prefer bank-branch or indoor machines.
- Check for loose panels on POS terminals.
Detection tools like skimmer scanners exist for businesses.
A visual guide to common tampering signs:

Legal and Ethical Ramifications
Possessing or using GSM data receiver skimmers violates laws such as 18 U.S.C. § 1029 (access device fraud) in the U.S., with penalties including up to 10–20 years imprisonment. Even purchasing “for research” risks charges. Ethically, these crimes victimize individuals, burden banks (costs passed to consumers), and fund organized crime.
The Future of Skimming and Payment Security
New technologies are reducing skimming risks. Biometric authentication, mobile wallets, and tokenized payments all eliminate the need to expose card data.
Banks are also upgrading ATM hardware to block unauthorized devices. At the same time, telecom providers track illegal GSM transmissions more closely.
As security improves, GSM skimming becomes more difficult and less profitable.
Practical Protection Strategies
- Use contactless payments (Apple Pay, Google Wallet) tokenized and encrypted.
- Prefer chip insertion over swipe; avoid fallback terminals.
- Enable transaction alerts and monitor accounts daily.
- Use credit cards over debit for purchases (better fraud protection).
- Report suspicious devices immediately to the merchant, bank, and authorities.
- For businesses: Regular inspections, security seals, anti-skimming hardware.
Conclusion
GSM data receiver POS/ATM skimmers exemplify criminal ingenuity in exploiting payment technology. By transmitting stolen data wirelessly and pairing with user-friendly (albeit illegal) software, they enable scalable fraud with minimal exposure. Awareness of their mechanics, combined with vigilant habits and modern payment methods, remains the strongest defense. As financial systems evolve toward biometrics and advanced encryption, these threats will diminish — but only if users and institutions stay proactive.
Stay alert, inspect terminals, and prioritize secure alternatives. Reporting potential skimmers helps dismantle these networks and protects everyone.

Extra Nuggets for those who read to the end of this topic: GSM Data Receiver POS/ATM Skimmer
Are you currently looking for a reliable and efficient ATM skimmer? Choose only the GSM Data Receiver! This wireless ATM skimming tool is designed to help you retrieve data wirelessly from ATM quickly and easily.
In Our online store, we offer all types of GSM Data Receivers and the software needed to operate them. Our blog is an excellent resource for anyone interested in learning more about this ATM skimming, including how to use it effectively, how to choose the best receiver for your needs, and much more.
We provide our customers with high-quality products and professional support. When you purchase a GSM Data Receiver atm/pos skimmer from Globalclonecards.com, you can be confident that you are receiving a best product in market that has been thoroughly tested and verified.
Our professional support team is always available to answer any of your questions and provide you with the assistance you need to get the most out of your GSM Data Receiver. Whether you are a seasoned professional or just getting started, we are here to help you succeed in ATM skimming industry.
So if you are in the market for a reliable and most popular ATM skimming tool, look no further than the GSM Data Receiver. Contact us today to learn more about our products and services and to find out how we can help you take your ATM skimming skills in top level. Now you will be able create skimming card copies without even touch a ATM.