Introduction
ATM skimming remains one of the most persistent and damaging forms of financial fraud, affecting millions of users worldwide each year. Among the most dangerous variants are GSM data receiver ATM skimming devices compact, wireless-enabled tools that allow criminals to capture card data and PINs remotely without needing to revisit the compromised machine. By integrating Global System for Mobile Communications (GSM) technology, these devices transmit stolen information via SMS or data packets directly to the fraudster’s phone, dramatically reducing their exposure to detection.
This article educates readers on the mechanics, evolution, and dangers of GSM data receiver skimmers, drawing from cybersecurity reports, law enforcement insights, and documented cases. While the technology itself is neutral, its criminal application is illegal and carries severe penalties, including federal charges for wire fraud, identity theft, and conspiracy. Understanding these devices empowers users to spot risks, adopt better habits, and contribute to safer financial ecosystems. Global skimming incidents continue to cost billions annually, with recent enforcement actions in 2025 recovering hundreds of devices and preventing massive losses.

GSM Data Receiver ATM Skimming Device
A GSM Data Receiver ATM Skimming Device targets card data through hidden digital traps.
It connects to illegal skimming hardware placed on payment machines.
However, modern fraud grows fast and becomes harder to detect.
Therefore, awareness becomes the first line of defense.
Banks, retailers, and customers face rising digital risks.
Meanwhile, criminals use wireless tools to steal card information.
Because of this trend, financial safety now demands better education.
This guide explains the technology in a clear and safe way.
What Is a GSM Data Receiver in ATM Skimming
A GSM data receiver collects stolen data through mobile networks.
It links to a concealed skimmer installed on an ATM.
Afterward, the device sends captured details to remote operators.
This wireless method avoids physical retrieval.
As a result, criminals reduce their exposure.
However, the signal also creates traceable footprints.
Therefore, banks monitor networks for suspicious activity.
The Basics of ATM Skimming and the Role of GSM Technology
Traditional ATM skimmers are small electronic overlays or inserts placed on or inside card readers to copy the magnetic stripe data as users insert or swipe cards. To complete fraud, criminals also need the PIN, often captured via a hidden pinhole camera or fake keypad overlay. Early skimmers required physical retrieval a risky step that exposed thieves to surveillance or patrols.
GSM integration changes everything. A GSM data receiver is essentially a skimmer equipped with a cellular modem (using a standard SIM card) that sends captured data in real time. This wireless capability eliminates return visits, making operations safer and more scalable for organized crime groups.
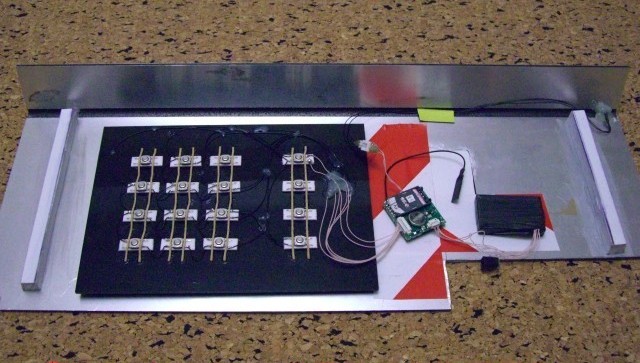
These devices typically include:
- A card reader module that intercepts magnetic stripe (or sometimes chip) data.
- A separate PIN capture component (camera or overlay).
- A GSM module with antenna for transmission.
- Battery power for days or weeks of operation.
Data is often sent as encrypted SMS messages or via GPRS/3G connections to a remote server or phone. Some advanced models store thousands of records locally as backup.
Here’s a visual example of a classic GSM-enabled ATM skimmer setup, showing the card reader overlay and attached GSM components:
This image, from early documented cases, illustrates how seamlessly these devices blend with legitimate ATM hardware.
Another view highlights the back of a PIN pad overlay with integrated GSM transmission:
The compact design and cellular connectivity make GSM skimmers far more efficient than Bluetooth or wired alternatives.
How GSM Data Receiver ATM Skimming Devices Work Step by Step
- Installation Phase Criminals target standalone or poorly monitored ATMs (convenience stores, gas stations, or lobbies). Installation takes seconds to minutes: the skimmer overlays the card slot, while a fake keypad or tiny camera captures keystrokes. A SIM card is inserted into the GSM module, often hidden inside the machine or nearby.
- Data Capture When a user inserts their card, the skimmer reads the magnetic stripe (track 1 and 2 data: card number, expiration, CVV). For PIN capture, the camera records the keypad or the overlay logs keystrokes.
- Wireless Transmission The GSM receiver immediately forwards the data via text message or data packet. Some models batch transmissions to conserve battery or avoid network flags. Range isn’t an issue global cellular coverage allows reception from anywhere with signal.
- Exploitation Fraudsters use the stolen data to clone cards (magnetic stripe duplicates), perform cash-outs at other ATMs, or sell dumps on dark web markets. With PINs, full account takeover is possible.
This process bypasses many traditional safeguards. As one expert analysis noted, GSM eliminates the “second trip” risk — a key vulnerability in older skimmers.
A close-up of an advanced GSM skimmer module demonstrates the tiny electronics involved:
Evolution and Modern Variants
GSM skimmers emerged prominently around 2010, revolutionizing fraud due to their remote access. Early models used basic SMS; later versions added encryption, longer battery life, and even infrared relays for insert-style skimmers (ultra-thin devices inside the reader slot).
While EMV chips reduced magnetic stripe cloning success in many regions, fallback attacks persist where terminals allow stripe use. Contactless skimmers and shimmers (chip-focused) have appeared, but GSM remains popular for its reliability in transmitting both card data and PINs.
Recent trends show hybrid attacks combining GSM with other tech, like infrared for short-range data pulls from insert skimmers.
How ATM Skimming Technology Works
ATM skimming relies on hidden reading devices.
These devices capture card stripe data during normal use.
Meanwhile, a tiny camera or overlay records PIN entries.
Afterward, the GSM module transmits the stolen data.
It sends information through standard mobile frequencies.
Therefore, criminals receive details in real time.
However, financial institutions use advanced detection systems.
These systems track unusual network signals near ATMs.
As a result, many attacks fail.
Real-World Cases and Prevalence in Recent Years
GSM-style wireless skimmers have featured in numerous high-profile busts. In 2025, U.S. Secret Service operations across states removed over 400 skimming devices, preventing more than $400 million in fraud. Agents inspected thousands of terminals, highlighting the scale of organized rings.
Notable examples include:
- Romanian nationals convicted in multiple states for installing skimmers on ATMs, using wireless transmission to harvest data.
- A suspect in Prince George’s County caught on camera placing devices; investigators recovered 45 skimmers in 2025 alone.
- Cases in Virginia, Maryland, and Pennsylvania where skimmers targeted convenience store ATMs, often with hidden cameras.
In one documented setup, fraudsters used GSM to send stolen tracks instantly, enabling rapid cloning and cash-outs before victims noticed irregularities.
A typical hidden camera used alongside GSM skimmers for PIN capture:
These incidents underscore that even in chip-dominant eras, legacy stripe vulnerabilities and insider placements keep skimming alive.
Detection and Warning Signs
Spotting GSM skimmers is challenging due to their discreet design, but vigilance helps:
- Visual Inspection — Tug gently on the card reader; legitimate ones don’t move. Look for misaligned bezels, extra bulk, or scratches.
- Keypad Anomalies — Fake overlays feel thicker or looser; cover your hand when entering PINs to block cameras.
- Behavioral Cues — If the machine feels “off” or transactions fail oddly, abort and report.
- Location Risks — Avoid standalone ATMs in remote or high-traffic non-bank locations.
Advanced detectors exist, but consumer-level awareness remains key.
An example of a skimmer detection tool for reference:
Legal, Ethical, and Societal Impact
Possessing, installing, or using GSM data receiver skimmers violates federal laws (e.g., 18 U.S.C. § 1029 for access device fraud), with penalties including years in prison and massive fines. Even purchasing for “testing” risks conspiracy charges.
Ethically, these crimes erode trust in banking, burden victims (especially vulnerable groups), and drive up costs passed to consumers. Organized groups often fund broader criminal activities.
Why GSM Receivers Attract Criminal Networks
Wireless transfer offers speed and distance.
Criminals avoid visiting crime scenes.
Therefore, they reduce the chance of being caught.
However, this convenience also leaves digital trails.
Network providers detect strange data bursts.
Consequently, law enforcement can trace signal origins.
Common Places Targeted by Skimming Devices
High traffic ATMs attract more fraud attempts.
Gas stations and small retail kiosks also face risk.
However, modern terminals now include anti-skimming sensors.
Because of this upgrade, criminals move to weaker systems.
Therefore, staying alert remains essential.
Risks Created by GSM Data Receiver ATM Skimming Device
Stolen card data leads to financial loss.
Victims face account drains and identity misuse.
Moreover, banks suffer reputation damage.
Additionally, fraud increases transaction costs.
These costs later reach consumers.
Therefore, everyone shares the burden.
How Banks Detect Wireless Skimming Signals
Banks monitor radio frequencies around ATMs.
They search for suspicious GSM transmissions.
Moreover, they use anomaly detection software.
This software flags irregular data patterns.
As a result, security teams act quickly.
Therefore, many attacks stop before real damage occurs.
Legal and Ethical Perspective
Using skimming equipment remains illegal worldwide.
Laws punish possession and operation severely.
Moreover, financial crimes lead to long prison sentences.
Ethically, such acts harm innocent people.
They break trust in digital systems.
Therefore, society rejects such behavior.
How Consumers Can Stay Safe
Cover the keypad when entering your PIN.
Inspect card slots for loose parts.
Moreover, avoid ATMs that look damaged.
Use bank alerts for transactions.
These alerts notify you in real time.
Therefore, you can react quickly.
Additionally, use contactless payments when possible.
They reduce exposure to physical skimmers.
Role of Software in Fraud Prevention
Security software analyzes ATM activity.
It checks patterns and detects anomalies.
Moreover, it updates threat signatures.
Artificial intelligence improves accuracy.
Therefore, banks respond faster.
As a result, fraud rates drop.
Importance of Network Monitoring
Telecom companies also help.
They monitor GSM traffic for illegal use.
When they detect abnormal signals, they report them.
Therefore, cooperation increases safety.
This partnership protects consumers and banks.
Future of ATM Security
Biometric verification grows in popularity.
Fingerprint and facial recognition reduce card use.
Therefore, skimming becomes harder.
Blockchain also improves transaction integrity.
It adds transparency and traceability.
As a result, fraud loses ground.
Why Awareness Matters
Education empowers users.
Informed customers spot suspicious signs.
Therefore, criminals lose opportunities.
Banks also run awareness campaigns.
These programs teach safe ATM habits.
As a result, communities become more secure.
Protection Strategies: Actionable Steps
- Choose Secure ATMs — Use bank-branch machines inside lobbies with constant surveillance.
- Leverage Modern Tech — Prefer contactless payments (Apple Pay, Google Wallet) or chip insertion; avoid stripe swipes.
- Shield Your PIN — Always cover the keypad; be wary of shoulder surfers or cameras.
- Monitor Accounts — Enable transaction alerts; review statements frequently.
- Report Immediately — If suspicious, notify the bank, police, and use fraud hotlines.
- Additional Tools — Consider RFID-blocking wallets for contactless cards; use virtual card numbers online.
Businesses should conduct regular inspections and install anti-skimming tech like encrypted readers.
Conclusion
GSM data receiver ATM skimming devices represent a peak in criminal adaptation turning a simple cellular standard into a tool for efficient, low-risk fraud. By understanding their operation, evolution, and countermeasures, individuals and institutions can significantly reduce vulnerability. As payment tech advances toward biometrics and tokenization, skimming will persist in legacy systems, making awareness timeless. Stay alert, inspect before use, and report anomalies promptly small actions collectively starve these threats of success.