Introduction
In the realm of modern payment systems, EMV technology stands as a cornerstone of security, revolutionizing how we handle credit and debit card transactions. Standing for Europay, Mastercard, and Visa, EMV refers to the global standard for chip-based cards that embed microprocessors to store and protect sensitive data. At the heart of this ecosystem lies EMV software chip writers tools designed to encode, personalize, and manage data on these chips. While these software solutions play a vital role in legitimate financial operations, they have also become a magnet for scams and illicit activities, where fraudsters exploit the technology for card cloning and unauthorized transactions.
This article aims to educate readers on EMV software chip writers, providing a balanced view of their technical foundations, beneficial applications, and the shadowy side of misuse. By understanding both the innovations and the perils, consumers, businesses, and developers can better navigate the digital payment landscape. We’ll explore the mechanics, real-world examples, legal implications, and protective measures, all while emphasizing that any involvement in fraudulent activities is illegal and punishable. As cyber threats evolve, knowledge remains the best defense against exploitation, with global fraud losses from card scams reaching billions annually. Whether you’re a tech enthusiast, a business owner, or simply a card user, this deep dive will equip you with practical insights to stay secure.
Understanding EMV Technology: The Foundation
Before delving into EMV software chip writers, it’s essential to grasp the basics of EMV technology. Developed in the 1990s by Europay, Mastercard, and Visa, EMV was created to address the vulnerabilities of magnetic stripe cards, which were prone to skimming and cloning. Unlike magnetic stripes that store static data, EMV chips use dynamic authentication, generating a unique cryptogram for each transaction. This makes it exponentially harder for fraudsters to replicate card information.
EMV cards contain an embedded microprocessor that interacts with payment terminals via contact (insertion) or contactless (tap) methods. During a transaction, the chip communicates with the reader to verify authenticity, often requiring a PIN or signature for added security. This process, governed by ISO-7816 standards, ensures encrypted data exchange, reducing counterfeit fraud by up to 63% in some regions since its adoption.
The evolution of EMV has led to widespread global adoption, with benefits including seamless interoperability, support for mobile payments like Apple Pay, and integration with loyalty programs. However, as with any technology, its strengths can be targeted by sophisticated attacks, underscoring the need for ongoing education and vigilance.
To illustrate, here’s a close-up view of an EMV chip on a credit card, showcasing the small metallic square that houses the microprocessor:
This tiny component is what elevates card security beyond traditional methods.
What is an EMV Software Chip Writer?
An EMV software chip writer is a specialized program or suite of tools used to encode, read, and write data onto the microprocessor chips embedded in EMV cards. In essence, it facilitates the personalization and configuration of cards by injecting cryptographic keys, cardholder information (such as name, account number, and expiration date), and application data. These writers operate through connected hardware like card readers or encoders, communicating via application protocol data units (APDUs) as defined in EMV specifications.
Legitimately, this software is part of a controlled ecosystem managed by card issuers, banks, and certified manufacturers. It ensures cards comply with global standards, enabling secure transactions worldwide. For example, during card production, the software encodes data in a structured file system using ASN.1 and TLV (Tag-Length-Value) formats, which organize information hierarchically for efficient retrieval.
However, the term “EMV software chip writer” often surfaces in underground contexts, referring to tools like X2 EMV or EMV v8, which claim to allow users to write cloned data onto blank chips. These are not official products but rather illicit software peddled on forums, Telegram channels, and dark web markets, promising easy card cloning for fraudulent gains.
A typical EMV chip writer setup might include:
- Hardware Interface: A USB-connected reader/writer device that physically interacts with the card’s chip.
- Software Components: Modules for data encoding, key generation, and verification.
- Security Protocols: In legitimate versions, robust encryption to prevent unauthorized access.
Visualize a common EMV card reader-writer device, which connects to a computer for data operations:
Such devices are essential for both development and issuance but can be misused if obtained illicitly.
Legitimate Uses of EMV Software Chip Writers
In authorized environments, EMV software chip writers serve critical functions in the payment industry. Primarily, they are employed by financial institutions and card manufacturers for personalization during the card issuance process. This involves:
- Data Integration: Collecting cardholder details from databases and writing them securely onto the chip, including the primary account number (PAN) and expiration date.
- Key Injection: Embedding cryptographic keys that enable secure authentication during transactions.
- Application Loading: Installing EMV-compliant applications that define how the card behaves in different payment scenarios, such as contact or contactless.
Software development kits (SDKs) like Mastercard’s Contactless Reader SDK allow developers to build custom EMV solutions for point-of-sale (POS) systems, ensuring compliance and interoperability. Hosted solutions provide turnkey options for businesses, integrating EMV processing without heavy development.
Beyond issuance, these tools support testing and maintenance. For instance, payment processors use them to simulate transactions, verify chip integrity, and update firmware on terminals. In retail, EMV software enhances security by enabling chip-and-PIN verification, reducing liability for merchants under the EMV liability shift rules.
Mobile EMV readers, like those from PayTrace, allow field teams to accept chip cards securely via apps, qualifying for lower interchange rates. Overall, legitimate uses focus on fraud prevention, efficiency, and global standardization, benefiting ecosystems from banks to e-commerce.
Illicit Uses, Scams, and Associated Risks
Unfortunately, the power of EMV software chip writers has attracted criminal elements. Illicit versions are marketed as tools for “writing dumps” (stolen card data) onto blank chips, enabling cloned cards for fraudulent purchases. These are often sold on platforms like Reddit or Telegram for $50–$500, bundled with tutorials.
Scams operate on two fronts: direct fraud and deceptive sales. In direct fraud, criminals use shimming inserting thin devices into readers to capture chip data or bypass cloning to create counterfeit cards. Fallback fraud involves damaging chips to force magnetic stripe swipes, exploiting terminals that allow it.
Sales scams prey on aspiring fraudsters by offering fake software that doesn’t work or infects devices with malware. Buyers pay via crypto, only to receive useless files or nothing. Risks include financial losses, identity theft, and legal prosecution, as possessing such tools can lead to charges under wire fraud laws, with penalties up to 20 years.
A depiction of a credit card skimming device, often used in conjunction with illicit EMV tools:

This highlights the hardware criminals use to harvest data for writing onto chips.
How EMV Chip Writer Scams Unfold
Scams typically begin with data theft via shimmers or skimmers installed on ATMs or POS terminals. Captured “dumps” include track data from magnetic stripes or partial chip info. Fraudsters then use software like X2 to encode this onto blank Java Card Operating System (JCOP) cards, configuring ATR (Answer to Reset) and generating ARQC (Authorization Request Cryptogram) codes.
In retail scams, perpetrators insert fake-chipped cards, claim chip errors, and request swipes to bypass EMV security. Online, phishing emails pose as banks offering “EMV upgrades,” tricking users into revealing details.
These operations fund organized crime, eroding trust in payment systems and costing billions. Ethically, they harm vulnerable groups and inflate costs for honest users.
Legal and Ethical Implications
Using or distributing illicit EMV software violates laws like the Electronic Funds Transfer Act and can result in severe penalties. Even purchasing for “curiosity” risks complicity in fraud. Ethically, it undermines financial integrity, disproportionately affecting small businesses and consumers.
Governments and organizations like EMVCo enforce standards to combat this, but user awareness is crucial.
Protecting Yourself: Strategies and Best Practices
To mitigate risks:
- Inspect Devices: Check ATMs and readers for anomalies like loose parts or shimmers.
- Prefer Chip Transactions: Always insert or tap; avoid swipes if possible.
- Monitor Accounts: Enable alerts and review statements regularly.
- Use Virtual Cards: For online purchases, opt for tokenization services.
- Avoid Suspicious Offers: Report sites selling “EMV writers” to authorities like the FTC.
- Business Safeguards: Upgrade to EMV-compliant terminals and train staff on fraud detection.
- Educate and Report: Share knowledge and notify banks of suspicious activity promptly.
A graphic outlining warning signs of credit card fraud:
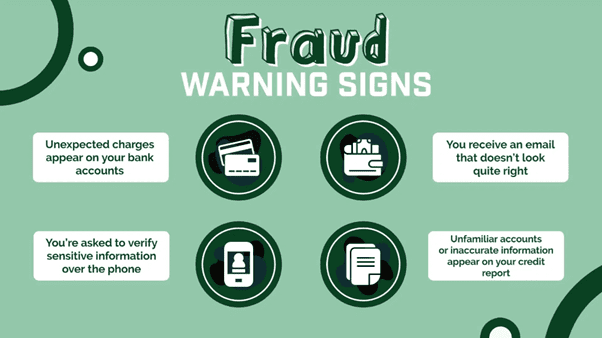
These visuals can help identify potential threats quickly.
For developers, use certified SDKs and comply with PCI DSS standards to avoid vulnerabilities.
Conclusion
EMV software chip writers embody the dual-edged sword of technology: invaluable for secure, efficient payments when used legitimately, yet perilous in the hands of scammers. By educating ourselves on their mechanics, applications, and risks, we can harness the benefits while minimizing dangers. As EMV evolves with biometrics and advanced encryption, staying informed ensures we remain ahead of threats. Remember, true security starts with vigilance—protect your data, report irregularities, and contribute to a safer financial world.
Understanding How the EMV Card Security System Works
Card Number:
In the past, payment by card number was the primary method, where the number was physically stamped on the card. The card was rolled on a device, and the number was manually entered into a database for record-keeping. At the end of the day or week, the data was collected and sent to the acquiring bank, which then requested the debiting of the funds from the cardholders through issuing banks. The three-digit verification code (CVV2/CVC2) on the back of the card served as a checksum to prevent errors during payment entry.
Nowadays, physical cards may not be required for payments. This is referred to as “card not present” and is commonly used for online payments. When entering the card number at a payment terminal, such as in hotels or businesses taking phone orders, it is known as PAN Key Entry. Contrary to popular belief, the Cardholder name field on the card is not checked by banks.

Magnetic Stripe:
The magnetic stripe on the card is susceptible to certain types of fraud, such as skimming at ATMs or double withdrawals in restaurants. Copying the magnetic stripe is relatively easy with a magnetic stripe reader/encoder. The cloned stripe can be used for payments in most supermarkets worldwide. To verify the cardholder, a signature on the receipt is required, which the cashier matches with the signature on the back of the card.
The information recorded on the card’s magnetic stripe includes the card number, expiration date, cardholder’s name, and a service code indicating the card’s functions and features. The verification code (CVV, CVC, CID) on the back of the card is calculated using cryptographic algorithms and serves as an additional security measure. The issuing bank verifies the magnetic stripe data and checks if the calculated CVV matches the transmitted value.
Chip/EMV:
Smart cards with embedded chips were introduced as a replacement for magnetic stripes in the 1990s, popularized by the EMV consortium (Europay, MasterCard, Visa). Smart cards utilize symmetric and public key cryptography to address the vulnerabilities of magnetic stripes. They provide three levels of protection: card authentication, payer verification, and transaction authorization.
Payer verification can be done using a PIN code or a signature. Offline and online PIN verification methods exist, and in some cases, no verification (NoCVM) is required for low-risk transactions. Additional methods, such as CDCVM or CWM, enable verification through the cardholder’s mobile phone.
Transaction authorization involves creating a payment cryptogram by the smart card. The card sends encrypted data to the payment terminal, including transaction details and internal card information. The issuing bank uses a hardware security module (HSM) to verify the cryptogram and check the PIN code if online verification is used.
It’s important to note that all three functions (authentication, verification, and authorization) must work together for a secure transaction. Without proper authentication or authorization, the transaction becomes high-risk.

Contactless Payments:
Contactless payments gained popularity in the mid-2010s as a fast and convenient payment method. However, they introduced their own security challenges. Legacy modes were initially implemented to allow new contactless cards to work on older payment terminals. These modes had lower security compared to EMV payments and modern contactless methods. Although initially intended for limited use, legacy modes were eventually phased out.
Different approaches were taken by Visa and MasterCard for contactless payments. Visa aimed to reduce payment time and decided to skip offline authentication, while MasterCard made it mandatory for added security. This led to differences in operation time and authentication requirements between the two payment systems.
Understanding the workings of the EMV card security system helps in comprehending the layers of protection and the advancements made to enhance. If you are interested place order now contact us